-
Everest Contact Forms Spam Protection: How to Stop Fake Entries in WordPress
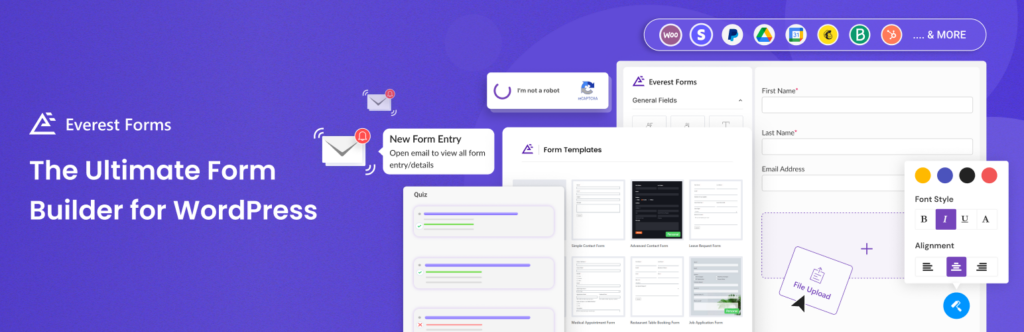
Everest Forms can be used for much more than a simple contact form. Many WordPress websites use it for inquiries, lead generation, bookings, quote requests, surveys, applications, payments, quizzes, file uploads, and customer feedback. That flexibility is useful for real visitors, but it also creates more entry points for spam. If an Everest form is
FEEDBACK LOG
The Latest
-
CVE-2023-4019 – Media from FTP < 11.17 - Author + Arbitrary File Access via Path Traversal
In a profound exploration of WordPress plugins, a chilling revelation has come to light. During meticulous testing, a high-impact vulnerability was unearthed within the Media from FTP plugin, specifically versions preceding 11.17. This alarming flaw exposes an avenue for attackers to exploit Path Traversal techniques, enabling unauthorized access to sensitive files and documents. The plugin…
-
CVE-2023-3814 – Advanced File Manager < 5.1.1 - Admin+ Arbitrary File/Folder Access via Path Traversal
In the realm of WordPress plugins, a severe security vulnerability has been unveiled. A comprehensive testing process revealed a critical flaw within the Advanced File Manager plugin, specifically versions up to 5.1.1. This vulnerability exposes a significant security lapse that can potentially allow unauthorized access to files and folders through Path Traversal techniques. Main info:…
-
We Have Reduced the Malware Code Analysis Time from 36 Hours to 10 Minutes
In case Security Malware Scanner detects a suspicious file, the file is sent for analysis and, earlier this analysis was done manually by our team. For 3 months now the files have been processed by our AI and the average analysis time has decreased from 36 hours to 10 minutes. However, we continue to double-check…
-
CVE-2023-4209 – POEditor < 0.9.8 - Settings Reset via CSRF
In our quest for a secure WordPress environment, a significant discovery has emerged. The POEditor plugin, a powerful translation tool, harbors a critical vulnerability. Prior to version 0.9.8, the absence of Cross-Site Request Forgery (CSRF) protection has exposed the plugin to potential manipulation by attackers. Main info: CVE CVE-2023-4209 Plugin POEditor Critical Medium Publicly Published…

