-
Everest Contact Forms Spam Protection: How to Stop Fake Entries in WordPress
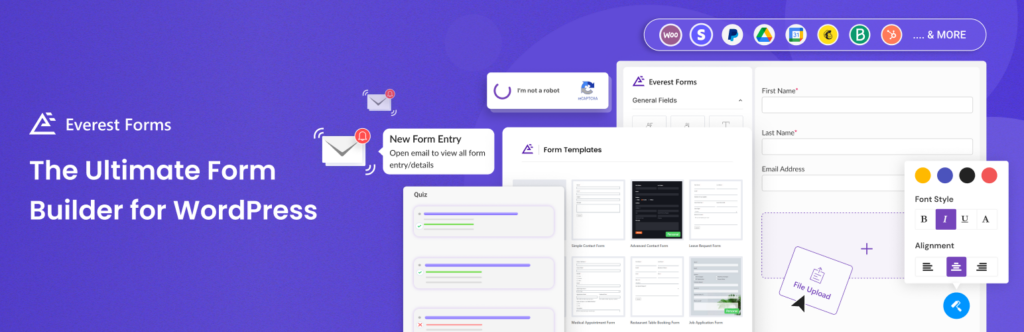
Everest Forms can be used for much more than a simple contact form. Many WordPress websites use it for inquiries, lead generation, bookings, quote requests, surveys, applications, payments, quizzes, file uploads, and customer feedback. That flexibility is useful for real visitors, but it also creates more entry points for spam. If an Everest form is
FEEDBACK LOG
The Latest
-
Flamingo Plugin new option – “Not Saving Spam Messages”
As you know, we have direct integration with the most popular contact form plugin – Contact Form 7. Also, you are probably familiar with the Flamingo – a message storage plugin, which doesn’t store submitted messages. Earlier, when using these two plugins simultaneously with CleanTalk Anti-Spam, messages recognized as spam would end up in the…
-
Attention CleanTalk Anti-Spam Users! Important Update Regarding Public Widget
We’re writing to inform you that the public widget for CleanTalk Anti-Spam will be removed from the plugin and no longer be supported after August 1, 2024. What does this mean for you? The public widget, which is typically displayed on public pages and demonstrates the number of spam attacks, is no longer considered compatible…
-
Critical Vulnerability Discovered in Gutenberg Blocks by Kadence Blocks Plugin
Our team at CleanTalk prioritizes the safety and security of the WordPress ecosystem. Through routine security testing, we’ve identified a critical vulnerability in the Gutenberg Blocks by Kadence Blocks plugin. This flaw poses a serious threat to WordPress websites, as it allows attackers to inject malicious code and potentially gain complete control. Understanding the Threat…
-
Mitigating WordPress.com API Vulnerability
Attention WordPress website owners! We’re excited to announce that the CleanTalk Security Plugin now effectively addresses a well-known vulnerability involving the WordPress.com API. This vulnerability, previously discussed here, allowed unauthorized actors to potentially trace administrator usernames through a public API endpoint. While disabling the REST API entirely would be ideal, it wasn’t always a viable…



