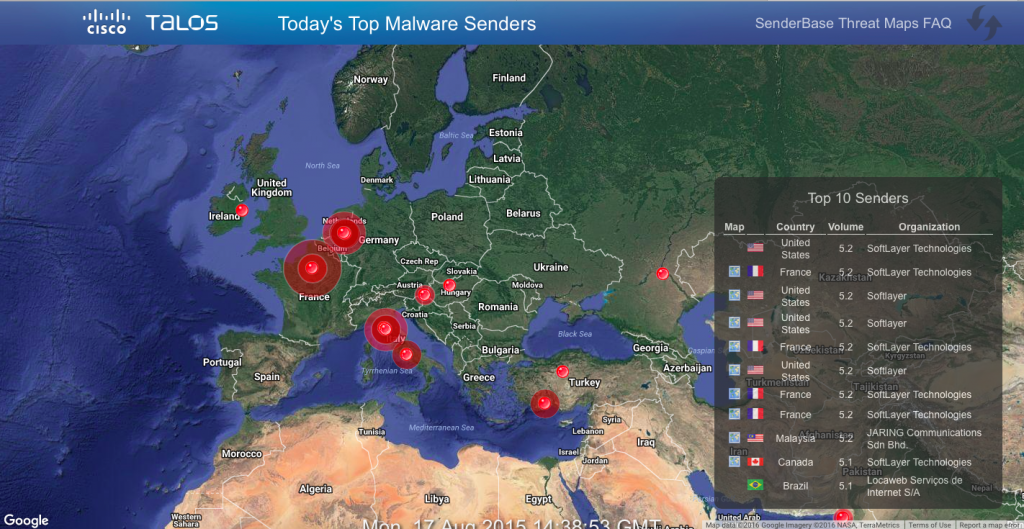
Those who visit our headquarters in San Jose (Cisco Systems) always amazes large video wall that displays a picture of attacks in real time with the ability to drill after touching certain areas of the screen.
However, like any map attacks, and I have collection of already 34, any such visualization is ineffective in real life. Show to superiors, show to journalists, to include in any movie… It’s all useful, but not very applicable in practice. Usually you have your own data sets that are generated by your protection. And you wonder what is happening in your network or directed at your network, but certainly not the beautiful card with the “ballistic missile attacks”, which are drawn by the absolute majority of companies offering visualization services attacks.
One of the solutions of arisen problems is an open source Toolkit OpenGraphiti, was developed by company OpenDNS, which is now part of Cisco. OpenGraphiti is a free engine for 3D visualization of data that can be used by analysts to display and analysis semantic networks. The presence of a private API allows you to effectively utilize OpenGraphiti for their own purposes, which, in the case of information security, include:
- visualization of botnets
- visualization of DDoS attacks
- visualization of spamming
- visualization the hacking campaigns
- visualization of the movement of malware/a hacker on the network
- visualization of vulnerabilities
- visualization of wireless devices, including unauthorized
- visualization of IoT devices
- visualization of the information flow within a corporate or departmental network, including in the analysis of e-mail
- visualization of the links in social networks
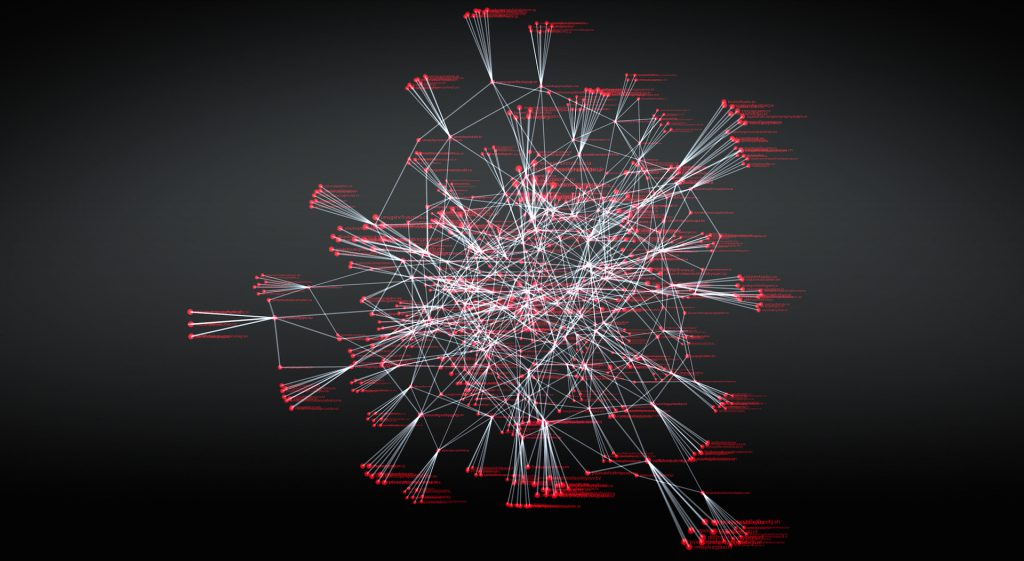
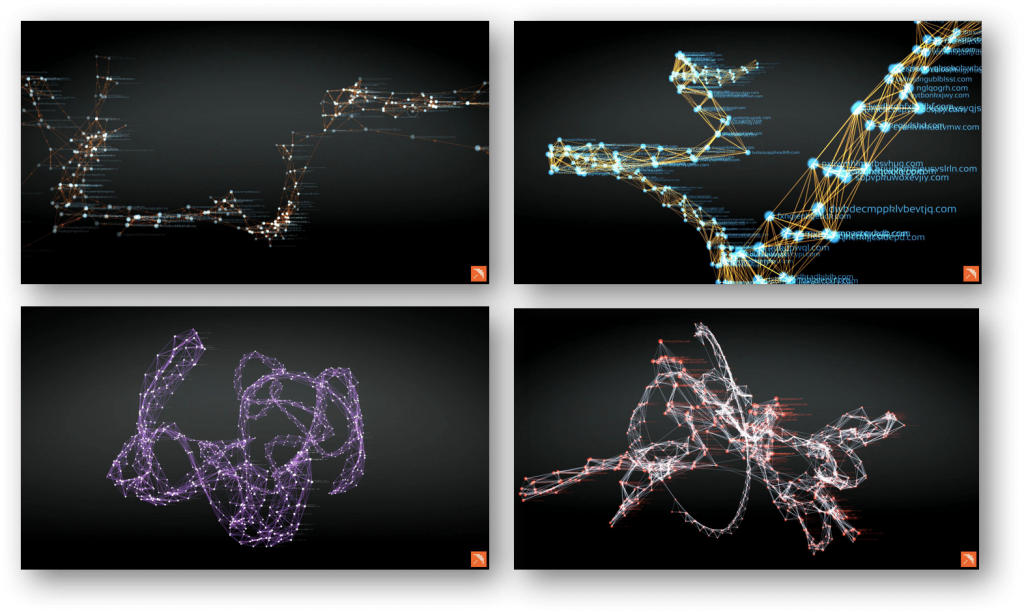
Here’s how, for example, looks the part of a semantic network spy campaign Dark Hotel, built with the help OpenGraphiti:
It is necessary to give some explanation of the color legend of this semantic network. Red displays the domains to which were sent the initial request, and the blue – the final point, to which was eventually forwarded the request through the intermediate nodes, marked in white. It is worth paying attention to these differences, as they once again demonstrate that banal “black” lists in a proxy, in systems to control access to the Internet or even in ITU, focused on the fight against the “red” nodes, completely ignoring the complex chain of interactions in malicious infrastructure.
And here’s the semantic network infrastructure ZeuS:
Finally, here is the spread of the Shellshock vulnerability:
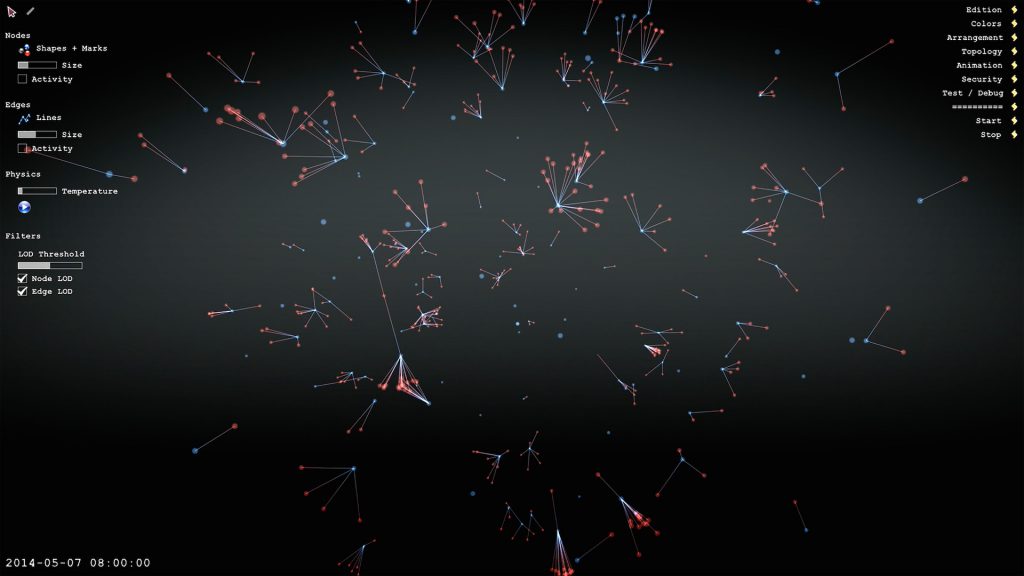
Of course, the best of the semantic network displays not static picture, and the dynamic changing map that can change its scale and detail, depending on the task facing analysts. For example, like this sees the website WikiLeaks and interaction with him:
A semantic network is an information domain model, having the form of a directed graph. This graph consists of vertices (nodes), which represent the studied entity.
To be more practical and to use a semantic network to the visualization of attacks and other anomalies, the entities or nodes of the graph can be considered different characteristics of servers and nodes in the network — Web, mail, NTP, SSH, etc. Another example – accounts in social networks or email. The edges or arcs of such a graph (connections between nodes) describe relationships between entities. Examples of such edges can be called the throughput, time, the number of connections/messages etc.
In the process of creating your own semantic network, we need to make a set of entities of interest of us, depending on purposes of analysis. For example, when analyzing of social networks, as entities (nodes) can be used as people and the company of interest of us. At the same time as the edges of the graph can be considered:
- Place of work
- Date of account creation (allows you to calculate bots)
- Account activity
- Religion
- Groups, which involve interested subjects
It is very easy using a semantic network to analyze the internal and external communications. As entities may be taken the e-mail addresses, and as relations between entities possible to take many different attributes:
- time of writing letters (or sending messages using messengers)
- the method of communication (e-mail, skype, Jabber, etc.)
- the device (personal or official)
If we want to analyze network communication, the quality of the studied entities we can take IP addresses, servers, hosts, ITU, routers, proxies, autonomous system, etc. And as relations (edges of the graph) can analyze used in network communication ports, hostname, country (geo-referencing), the autonomous system (AS), domain. Note, an autonomous system is mentioned twice — both as entity and as a relationship. Why is that? It all depends on what we want to analyze. If we are interested in how circulating traffic between different autonomous systems, they will be interested in us as entities, that is, the nodes of a semantic network. But if we are interested in how often we get attacked, then the autonomous system is transformed for us into a relationship, that is, edges of the graph.
The advantages of the OpenGraphiti, include:
- provide a context to search for various interactions between entities of interest to us, including various anomalies
- “the story” of your security based on Big Data
- the possibility of comparison of various attacks and campaigns
- assist in the attribution of attackers and identifying entry points for various violations of information security
- display “show” in real time, which allows to correlate the attack, or other violation with various news from the world of security (publication of information about vulnerabilities, new attacks, etc.).
If a little more attention to the first advantage, with the help of visualization we can identify the use DGA (Domain Generation Algorithms), which are used not only for marketing but also malware. Sites-day, domains which are created automatically and in large quantities for purposes of bypassing the “black” lists.
Once again, that OpenGraphiti is a free open source tool, requirements for which are fairly simple:
- MacOS или Linux
- Clang++ или g++
- Python 2.7.x
Installation and setup manual of OpenGraphiti is available on the website www.opengraphiti.com. By itself, the design is customizable and can be integrated into your monitoring centers (SOC), tying it with own data. So, for example, OpenGraphiti working on the OpenDNS website (Chrome is required):
It is obvious that with the growth of the volume of data grows and the complexity of the map. It can be controlled using grouping of entities or sampling. For example, I can visualize the entire network of millions of IP addresses (as in a Cisco network), and the sets of nodes grouped by various criteria — geographical location, belonging to the department, the importance of the node, etc. This allows you to not immediately dive into more detail and cover the picture of bird’s eye, followed by immersion in the area necessary to us at a given time.
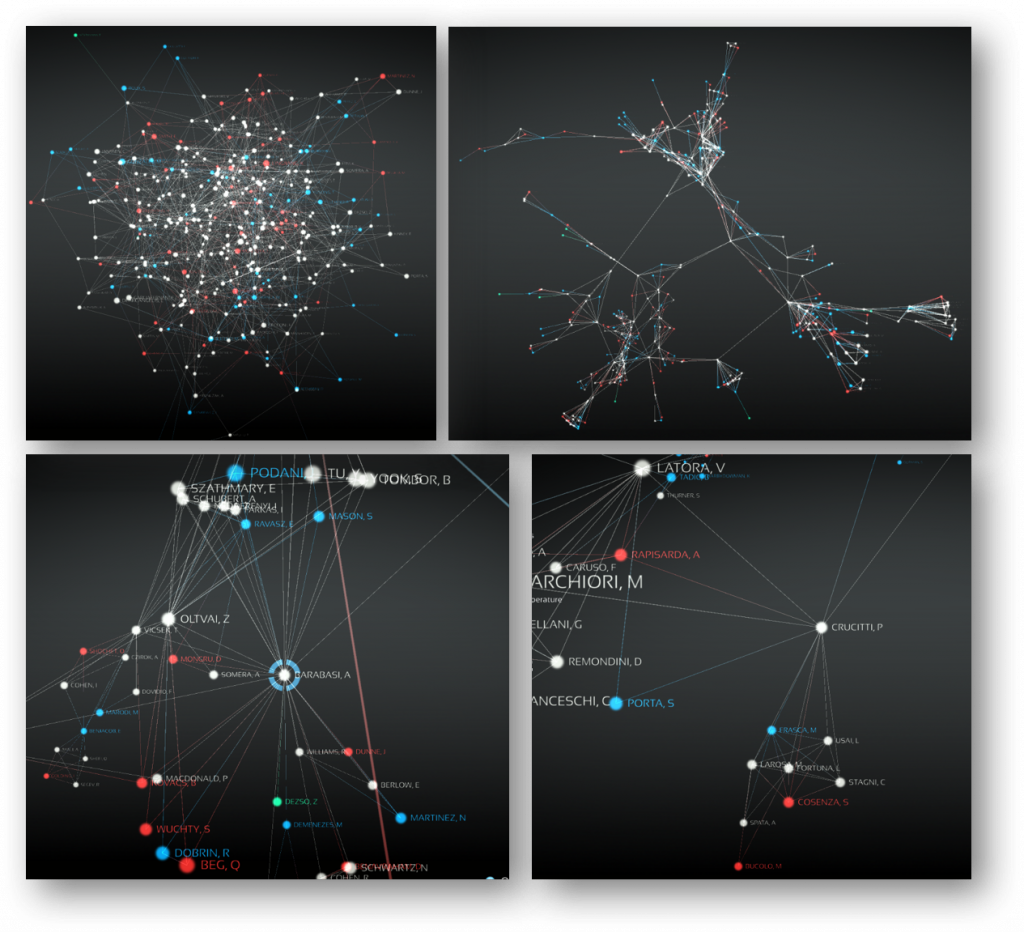
Here’s how, for example, looks a map of the botnet Zbot:
With the help of the zoom function on various parameters we can change the level of detail of the same map:
Why do we need visualization and why can’t we do the usual text or tabular representation of the data that are generated to us by available protection products? There is a good analogy. If you imagine that the human eye can transmit visual data to the brain at the speed of Ethernet, the reading of the text allows you to interact with the brain at speeds of dial-up. It is obvious that the work with textual information, namely it mainly operate of the most protection, today has a number of disadvantages, among which the main one is the speed of perception and detection of implicit dependencies. This is especially important when we deal with monitoring large volumes of frequently changing data. To achieve the desired effect with text data is difficult, and visualization, which in any case does not change the existing types of analysis is a good tool (provided that we know what and where to look).
In conclusion, I would like to note that today, in conditions when the intelligence services of information security is overloaded, it becomes very important to choose the right tools for visualization of large amounts of data, allowing you to see protected system that allows us to ask the right questions and get the right answers, which is the key to building the right information security strategy in the enterprise. And OpenGraphiti helps in solving this problem.
This text is a translation of the article “Визуализация атак, аномалий и нарушений информационной безопасности с помощью OpenGraphiti” published by Алексей Лукацкий @alukatsky on habrahabr.ru.
About the CleanTalk service
CleanTalk is a cloud service to protect websites from spam bots. CleanTalk uses protection methods that are invisible to the visitors of the website. This allows you to abandon the methods of protection that require the user to prove that he is a human (captcha, question-answer etc.).



Leave a Reply