-
Quform Spam Protection in 2026: How to Stop Fake Messages, Bot Submissions, and Junk Entries

If you use Quform on a WordPress website, spam will eventually become a real problem. Fake messages, bot submissions, junk inquiries, and low-quality entries can quickly fill your inbox and make genuine submissions harder to manage. This guide explains how to set up Quform spam protection using CleanTalk as the main filtering layer on your
FEEDBACK LOG
The Latest
-
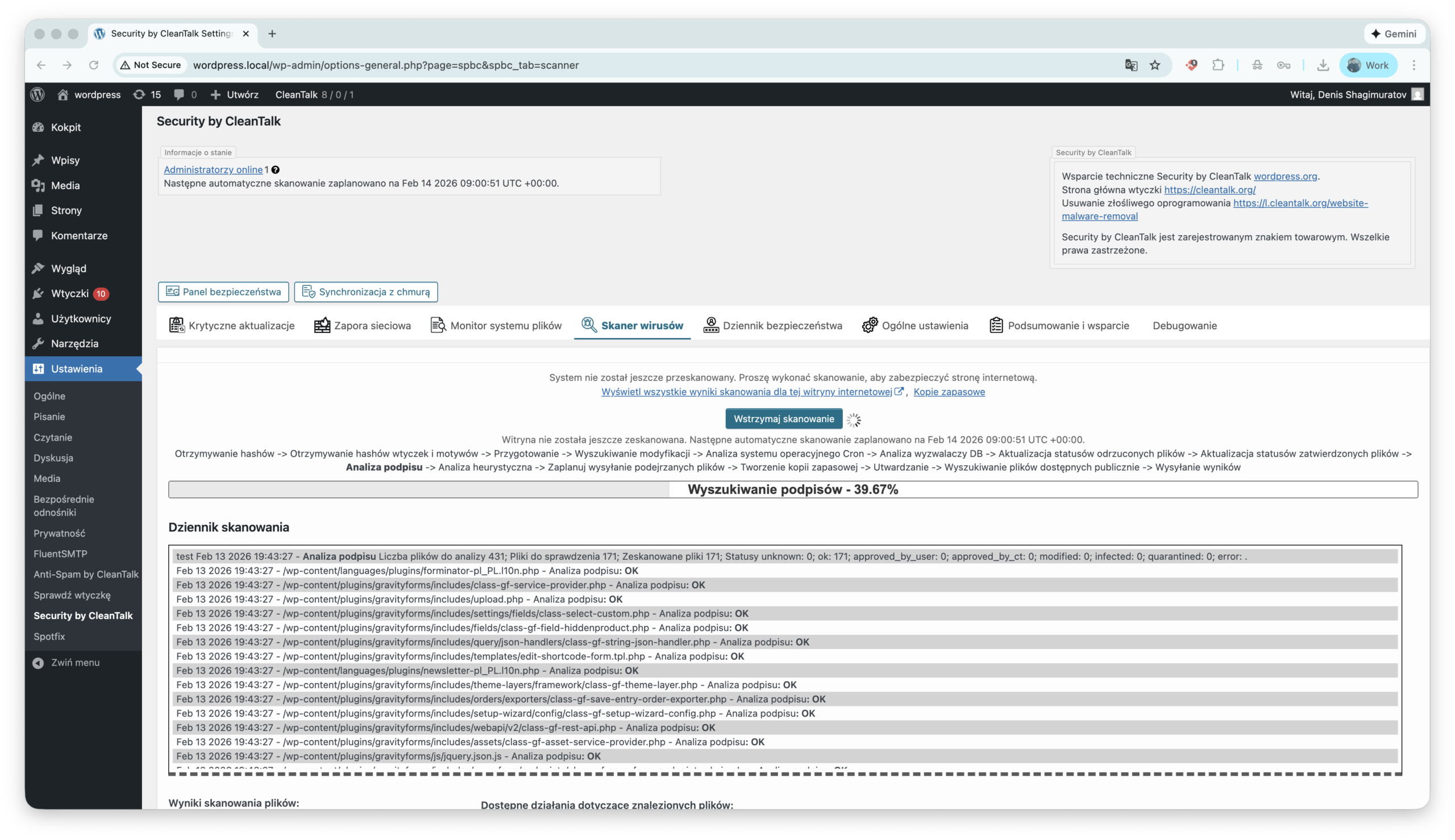
Wtyczka Security dla WordPress została przetłumaczona na język polski!
·
Z przyjemnością informujemy, że wtyczka Security od CleanTalk jest teraz dostępna w języku polskim. Tłumaczenie jest już gotowe do użycia. Szczególne podziękowania dla François-Xavier Bénard z zespołu WP Translations za cenne konsultacje dotyczące tłumaczenia! Masz pytania? Zadaj je w formularzu komentarzy!
-
About the email “[CleanTalk] Access key used on multiple websites”
Recently, some of our users received an email with the subject: “[CleanTalk] Access key used on multiple websites” The message informed you that your CleanTalk Access key was detected on more than one website within a 24-hour period and recommended changing the key if the activity looked suspicious. The notification looked like this: Subject: [CleanTalk]…
-
Our Client’s Review: BRNDTIME
We’re happy to share feedback from one of our valued clients — Christophe Thielens, founder of BRNDTIME. At CleanTalk, we truly appreciate hearing how our anti-spam solution helps agencies and businesses keep their websites clean, fast, and user-friendly. Reviews like this motivate our team to continue improving our technology and delivering invisible, reliable protection against…
-
Great plugin & support
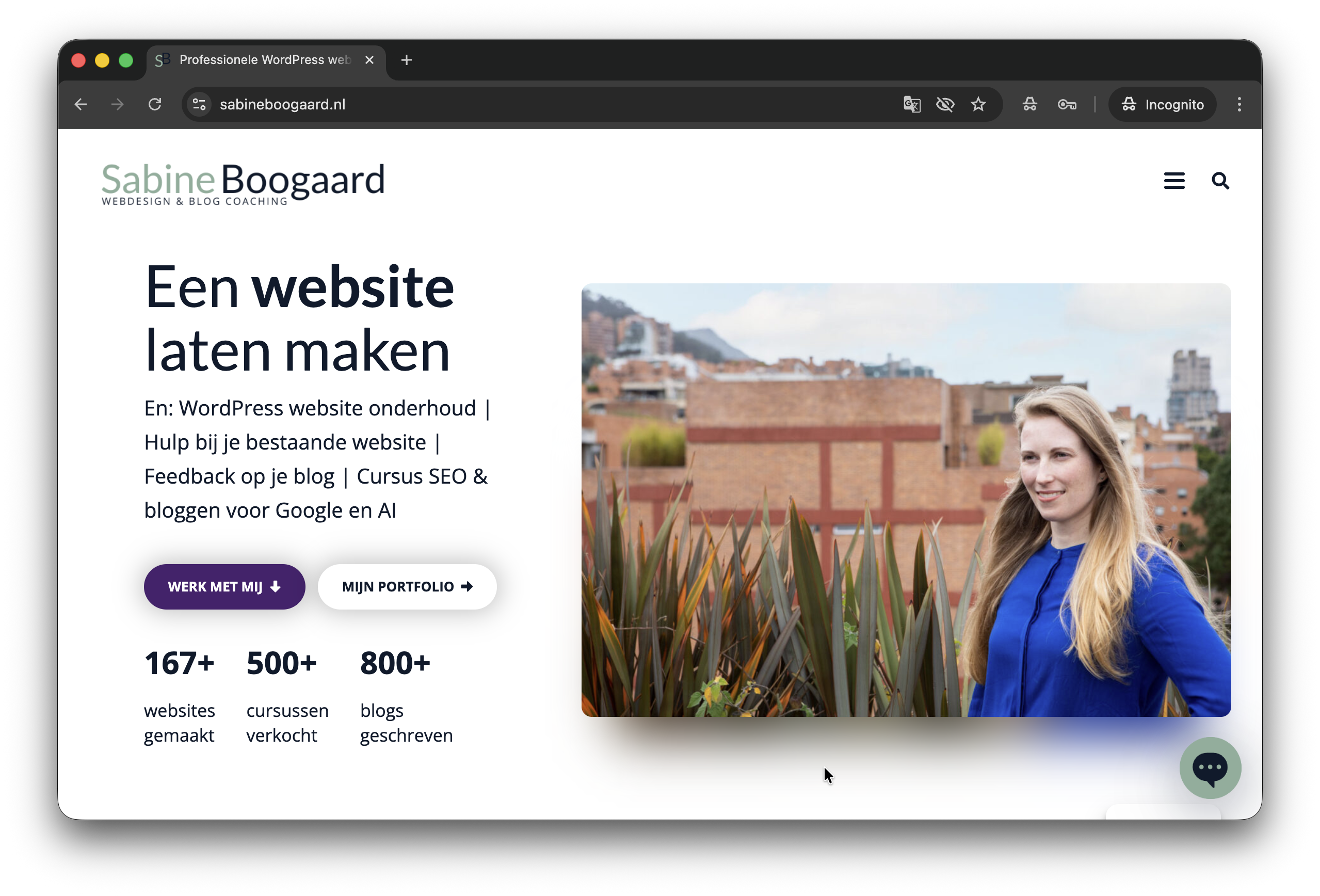
We continue to share stories of our clients and the new one is brought by Sabine from sabineboogaard.nl. To me this is the best security plugin. There are many options (like easily block IP-addresses and countries) and it’s very easy to monitor what’s happening on the website. I also love the automatic scans and reports. The…
![About the email “[CleanTalk] Access key used on multiple websites”](https://blog.cleantalk.org/wp-content/uploads/2024/10/attention1-1.png)