If you use HivePress to power a directory, classifieds, or marketplace website, you will eventually face spam – fake listings, bot registrations, and junk messages.
This guide explains how to set up HivePress spam protection using:
- the Anti-Spam plugin by CleanTalk with direct integration for HivePress, and
- additional tools like Google reCAPTCHA and basic moderation.
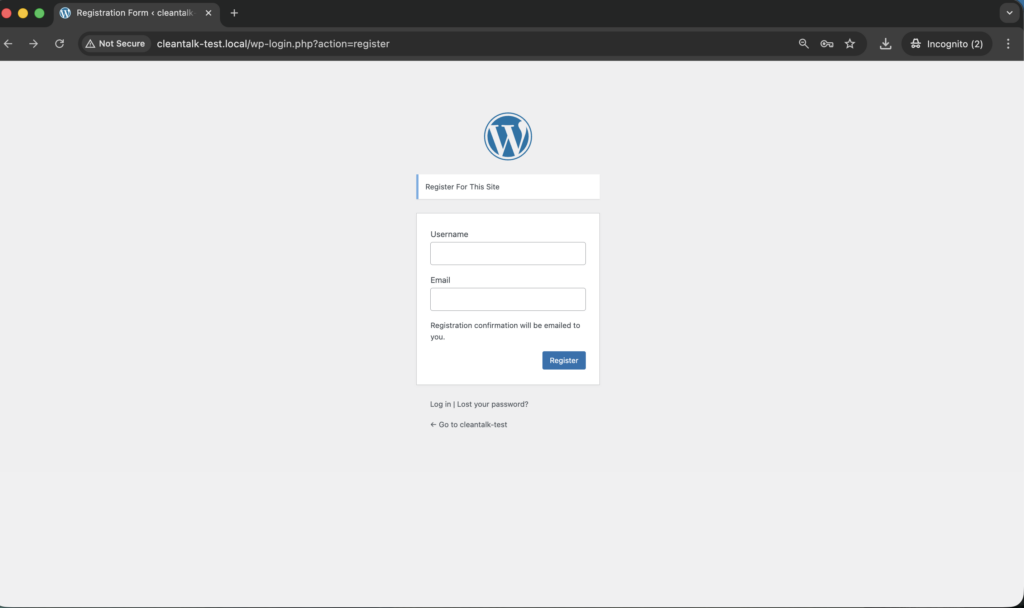
The integration now protects both:
- the registration form of HivePress (requests to /wp-json/hivepress/v1/users/), and
- the Add Listing form used to submit new listings.
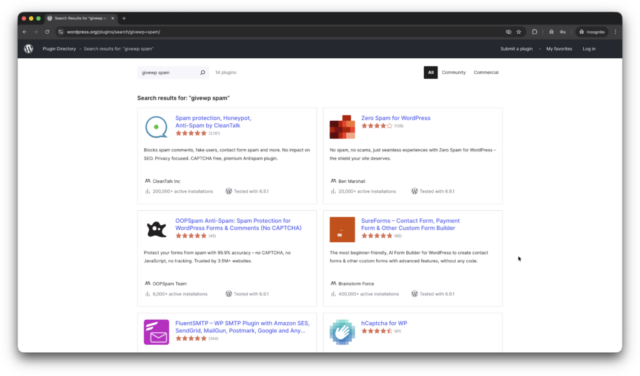
HivePress – Business Directory & Classified Ads Plugin
First, let’s take a quick look at HivePress itself and the types of sites you can build with it.
HivePress is a free and highly flexible WordPress plugin for building any type of directory or listing website: business directory, job board, classifieds, real estate catalog, rental marketplace, and more.
Out of the box HivePress provides:
- listing types, categories and custom fields;
- powerful search filters and location-based search;
- user accounts, ratings, reviews, private messages and favorites.
Because HivePress relies heavily on user-generated content and public forms, it quickly becomes a target for spambots. That’s why it is important to have a reliable HivePress spam protection setup from the beginning.
As WordPress.org shows, HivePress is currently used on over 10,000 websites and has 213 user reviews with an average rating of 4.9.
Plugin Homepage at wordpress.org | Website hivepress.io
Install HivePress to build business directories, classifieds, marketplaces and other listing websites.
You can set it up in just a few easy steps:
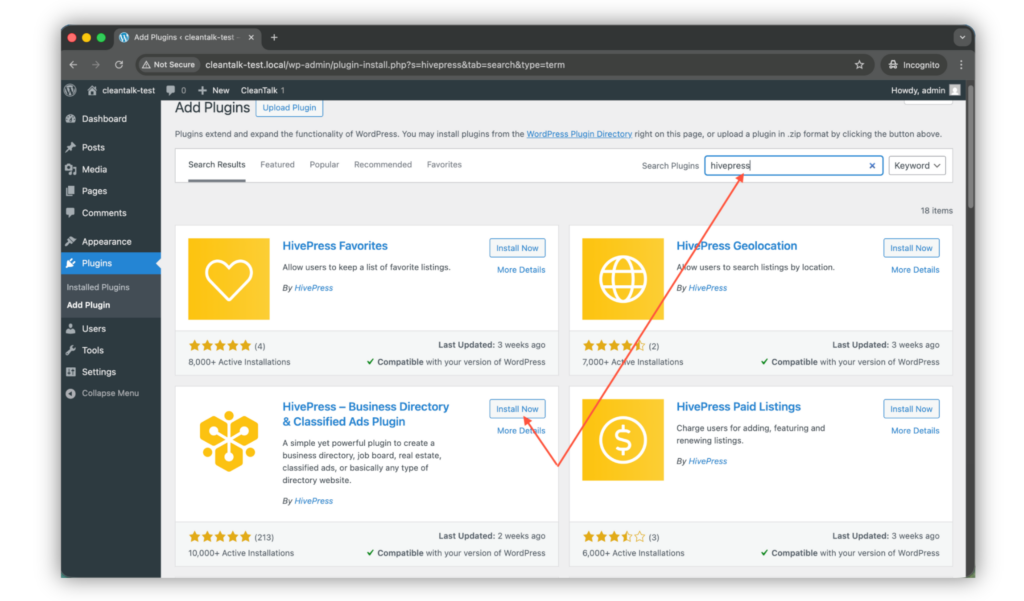
1. Search for the plugin in WordPress console -> Plugins -> Add plugin -> Search -> Type ‘hivepress‘
2. Install and Activate the plugin.
3. Add the very first listing in WordPress console -> Listings -> Add New.
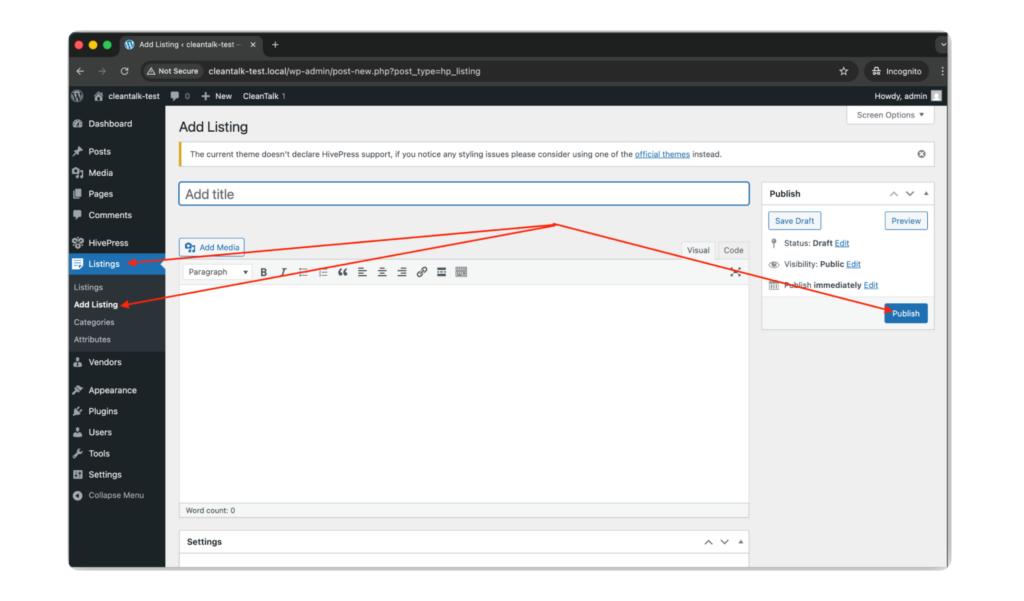
WordPress console -> Listings -> Add New -> add title, description, images and other fields -> Publish.
4. That’s all! Your first listing is live and HivePress is ready to use on your site.
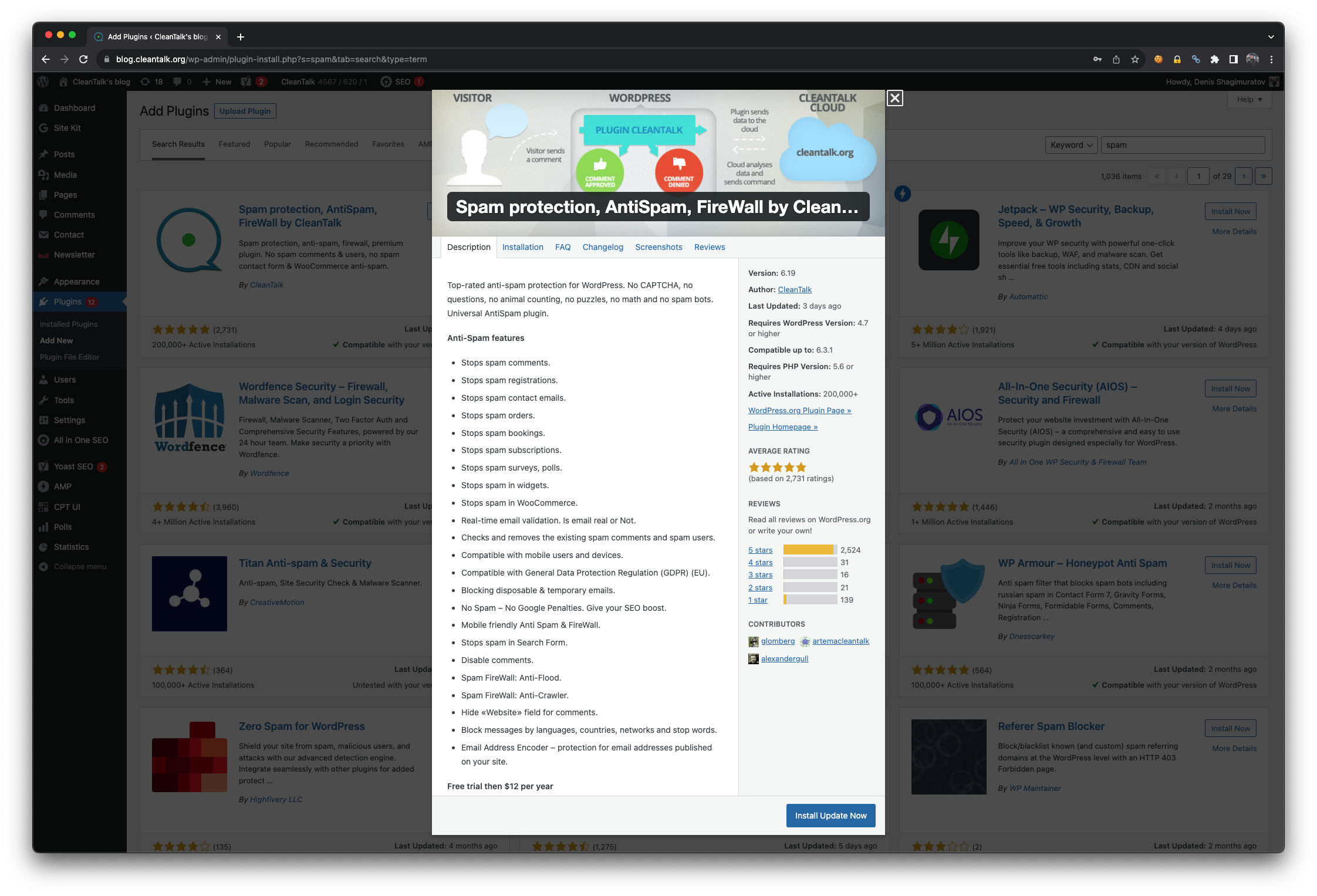
Anti-Spam plugin by CleanTalk for WordPress
The next tool we’re going to use is the Anti-Spam plugin by CleanTalk.
Here’s a short overview:
- CleanTalk is a cloud-based spam protection service for websites, founded in 2012.
- It automatically blocks spam without CAPTCHAs and doesn’t interrupt the user experience.
- Protects many types of forms: contact forms, payment forms, registrations, comments, surveys and more.
- Stops both automated bots and human spam submissions.
- Uses advanced filtering algorithms and a global spam detection network.
- Detects spam based on IP address, email address and user behavior.
- Lets you create custom filtering rules for specific cases.
- Allows blocking or filtering by IP, email and country.
- Works quietly in the background and is very easy to install and configure.
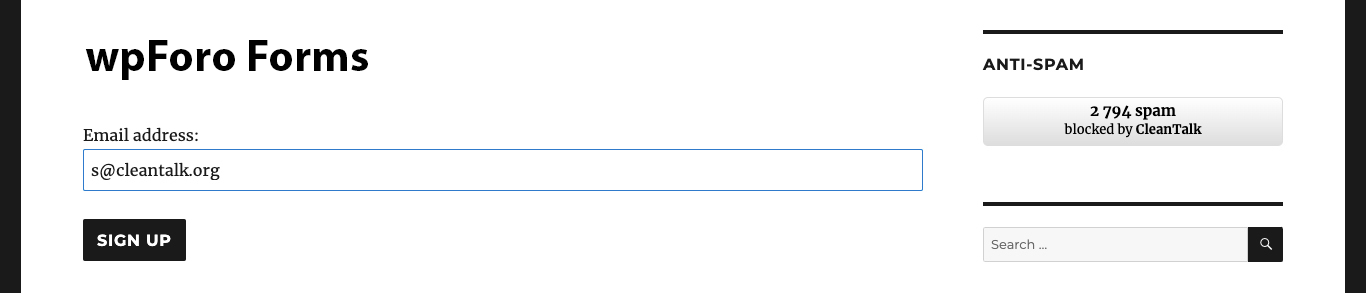
According to WordPress.org, Anti-Spam by CleanTalk for WordPress has over 200,000 active installations, with 3,168 reviews and an average rating of 4.7.
Plugin Homepage at cleantalk.org | Latest release at GitHub.com | Website cleantalk.org
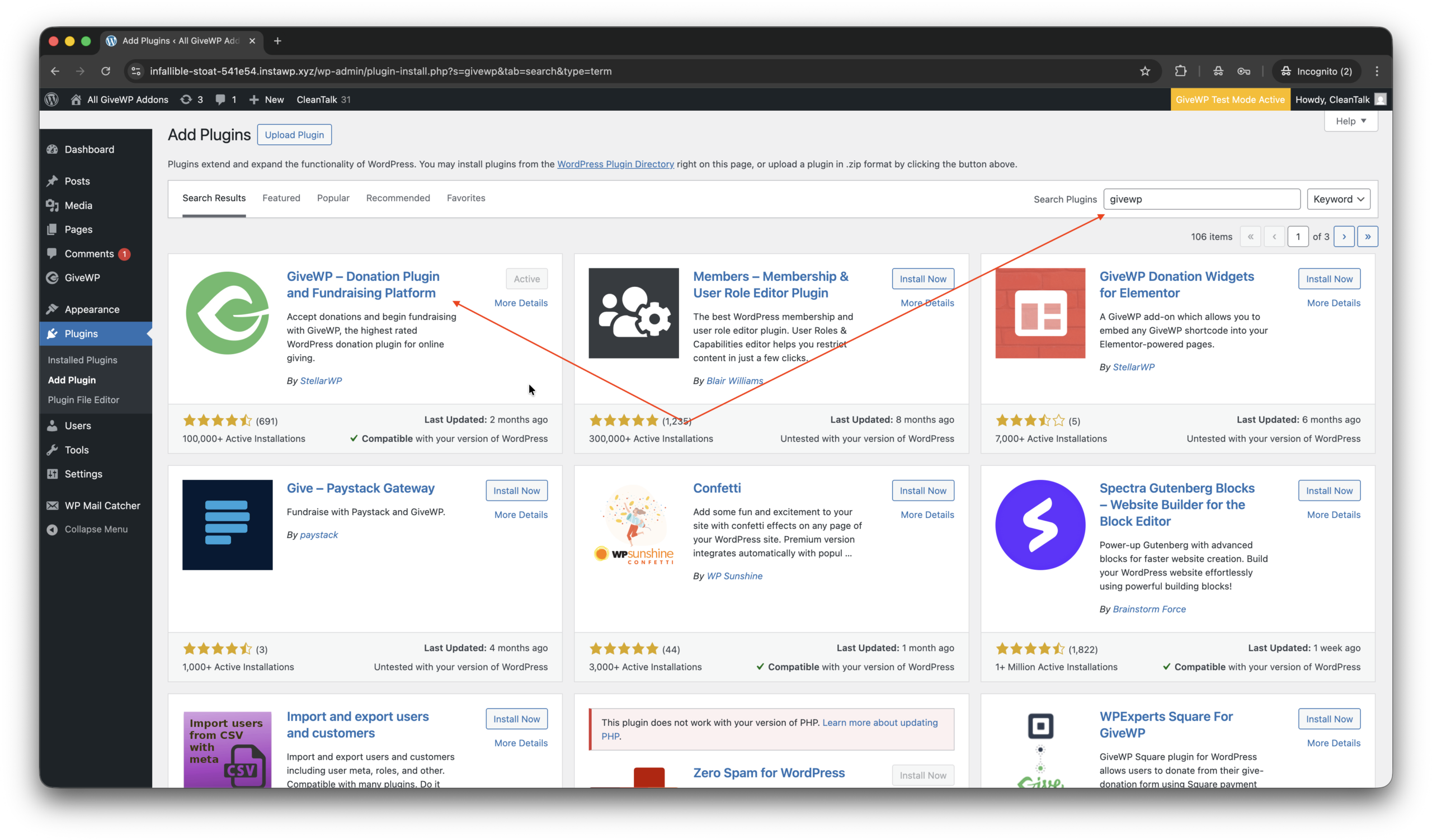
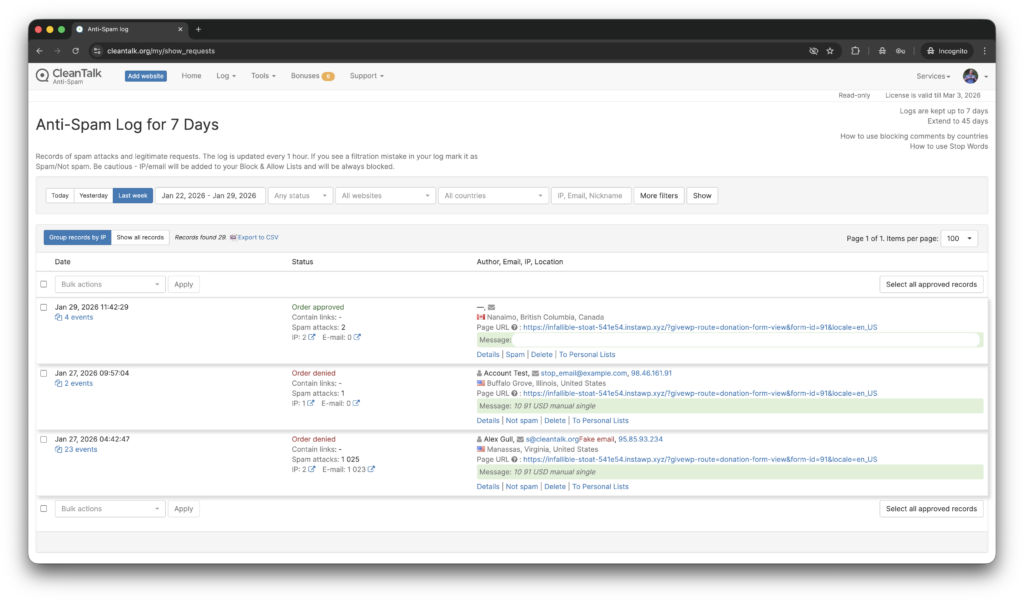
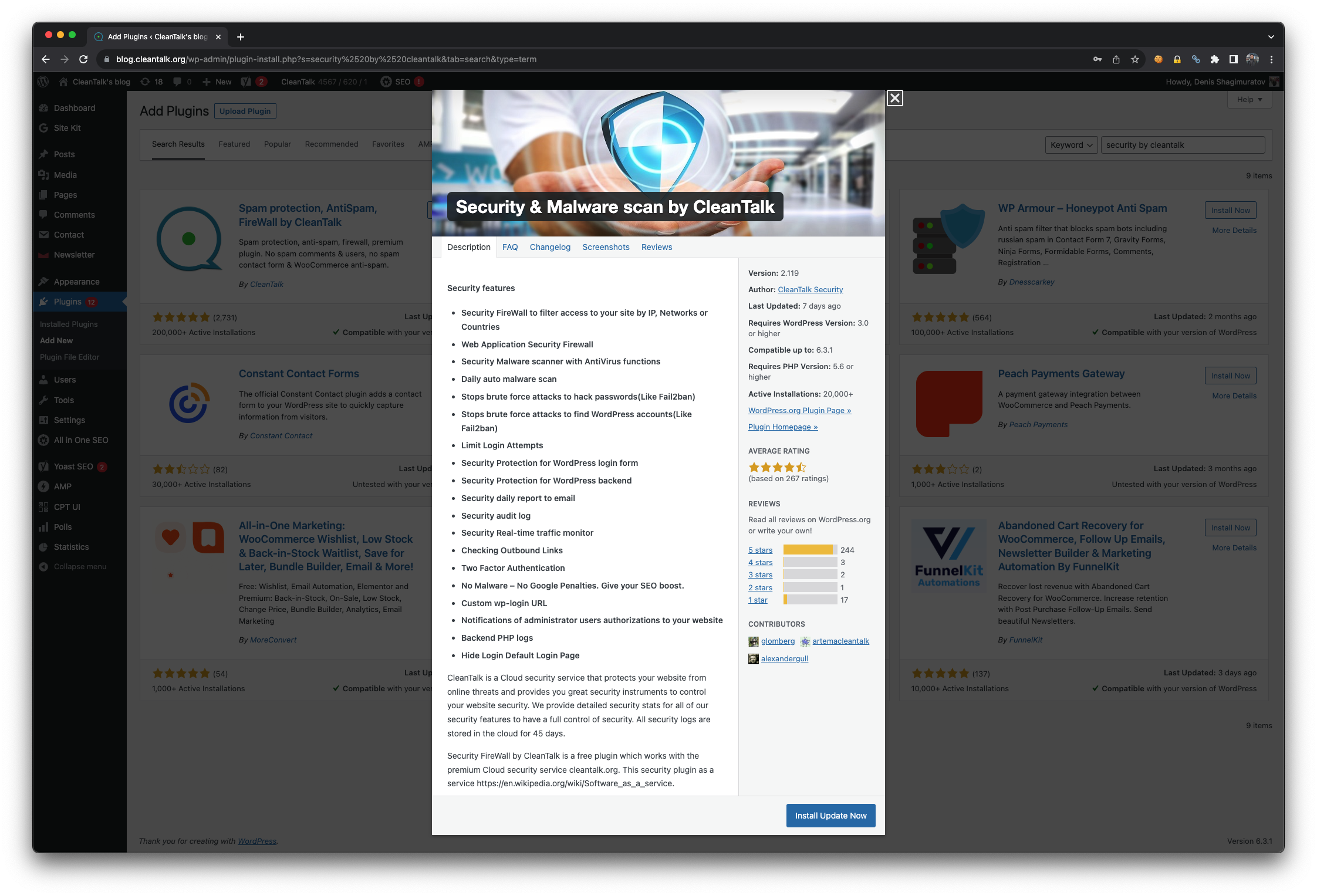
Install the CleanTalk Anti-Spam plugin
Show Instructions
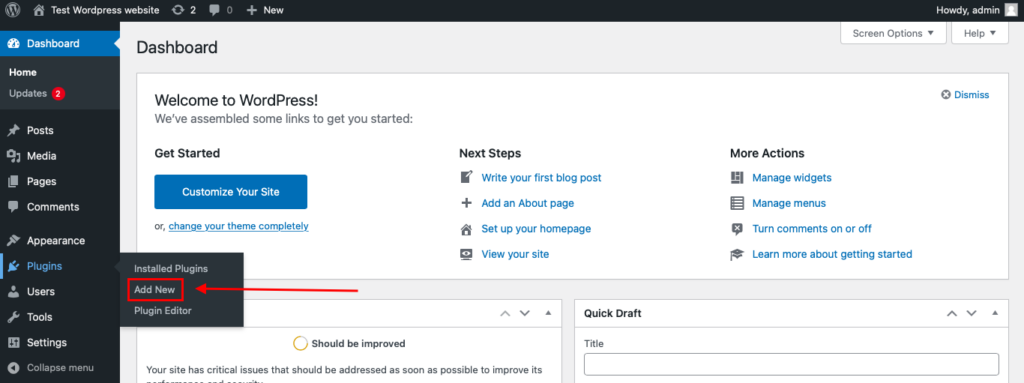
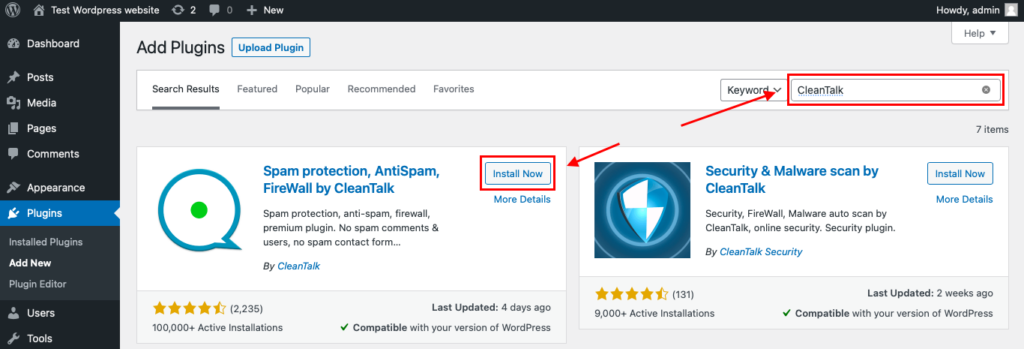
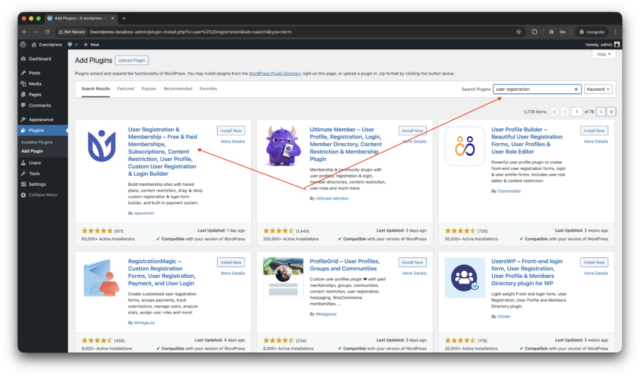
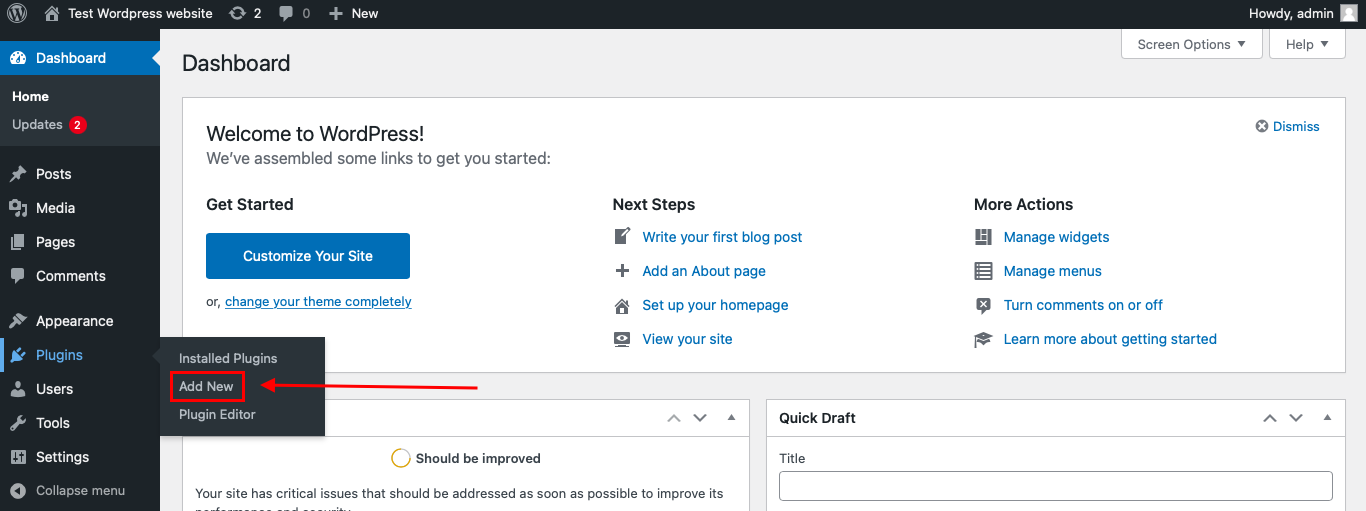
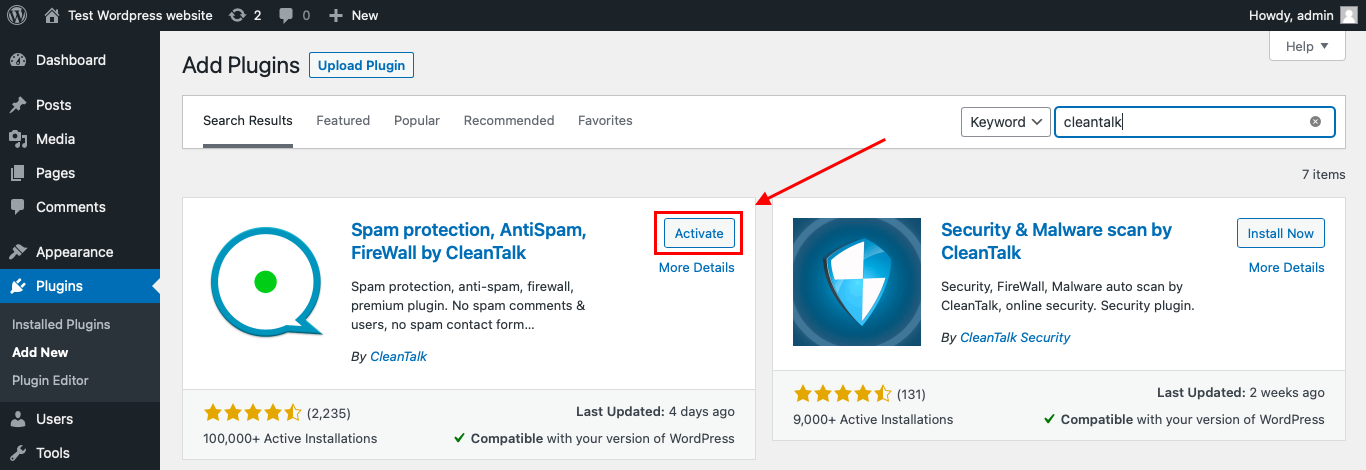
To install the Anti-Spam plugin, go to your WordPress admin panel → Plugins → Add New.
Then enter «СleanTalk» in the search box and click the Install button for «Spam protection, Anti-Spam, FireWall by CleanTalk».
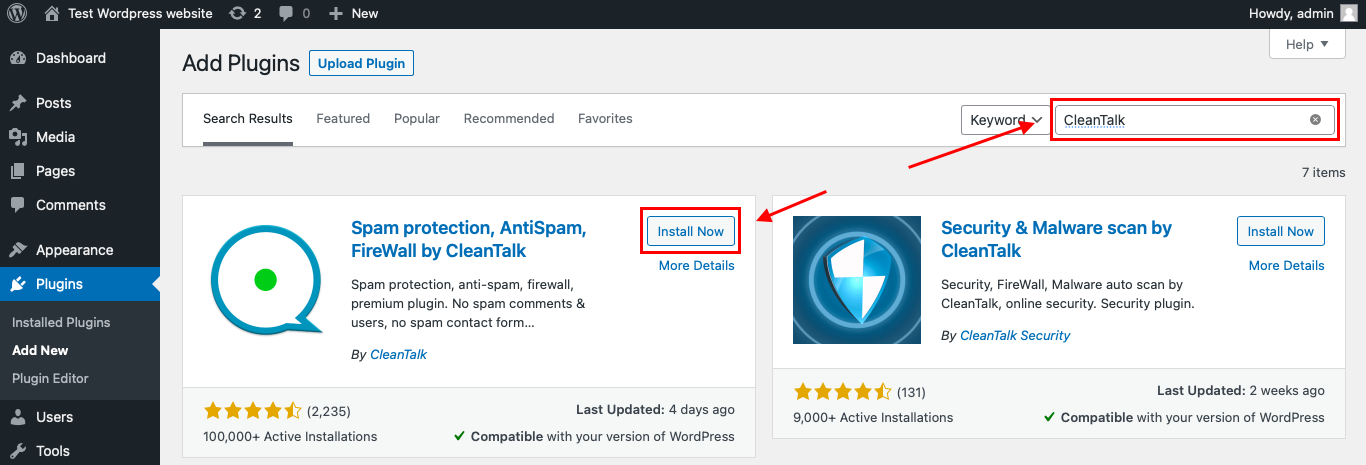
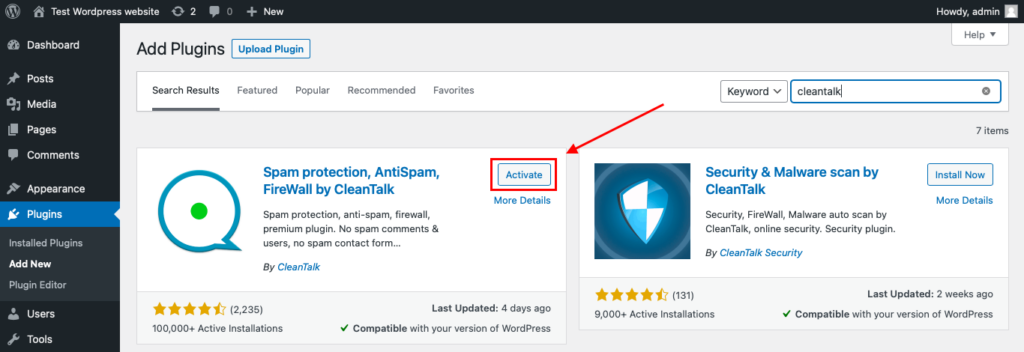
After installing the plugin, click the «Activate» button.
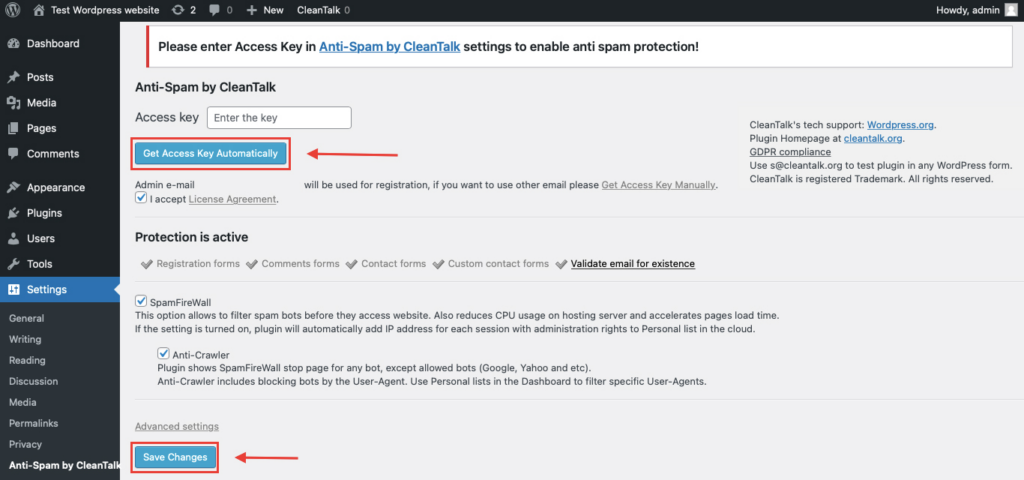
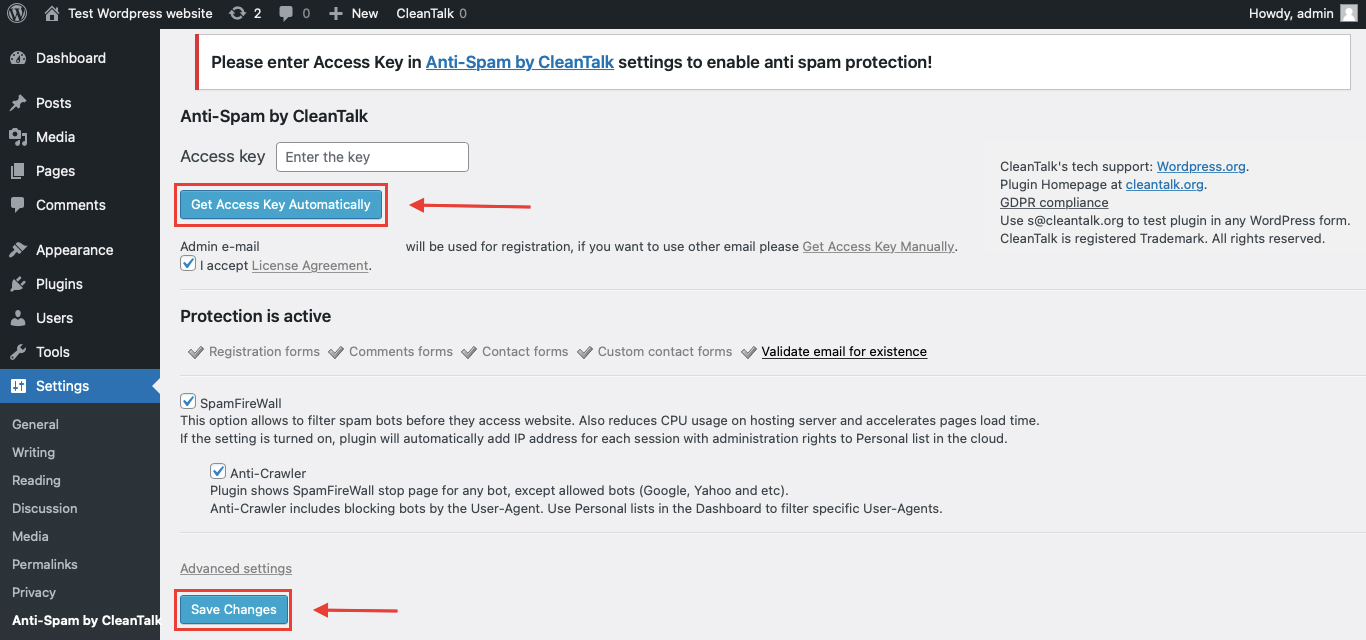
After it is done go to the plugin settings and click the «Get Access Key Automatically» button. Then just click the «Save Settings» button.
That’s it! From now you know how to completely protect your HivePress from spam.
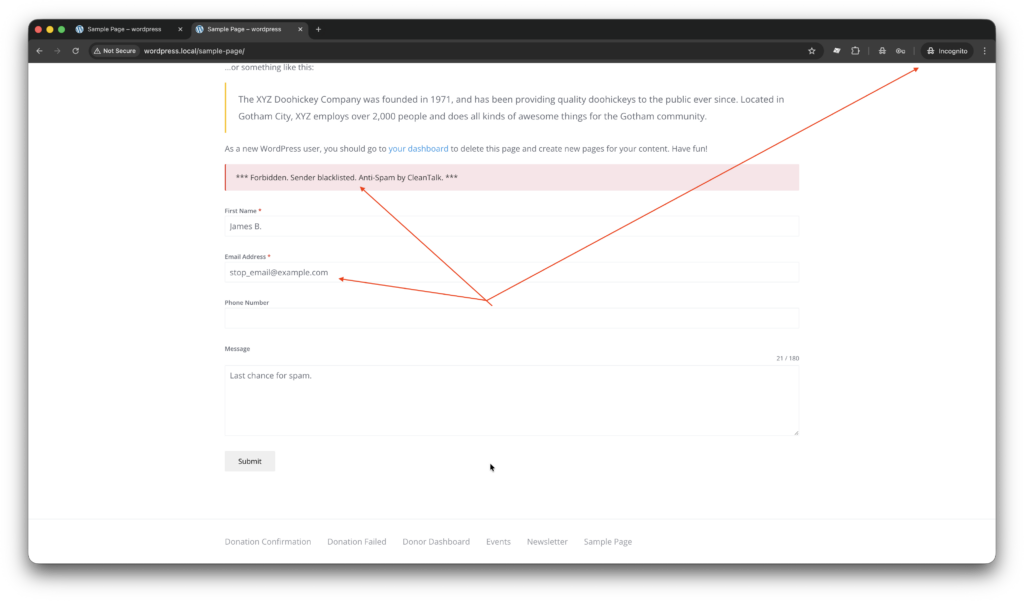
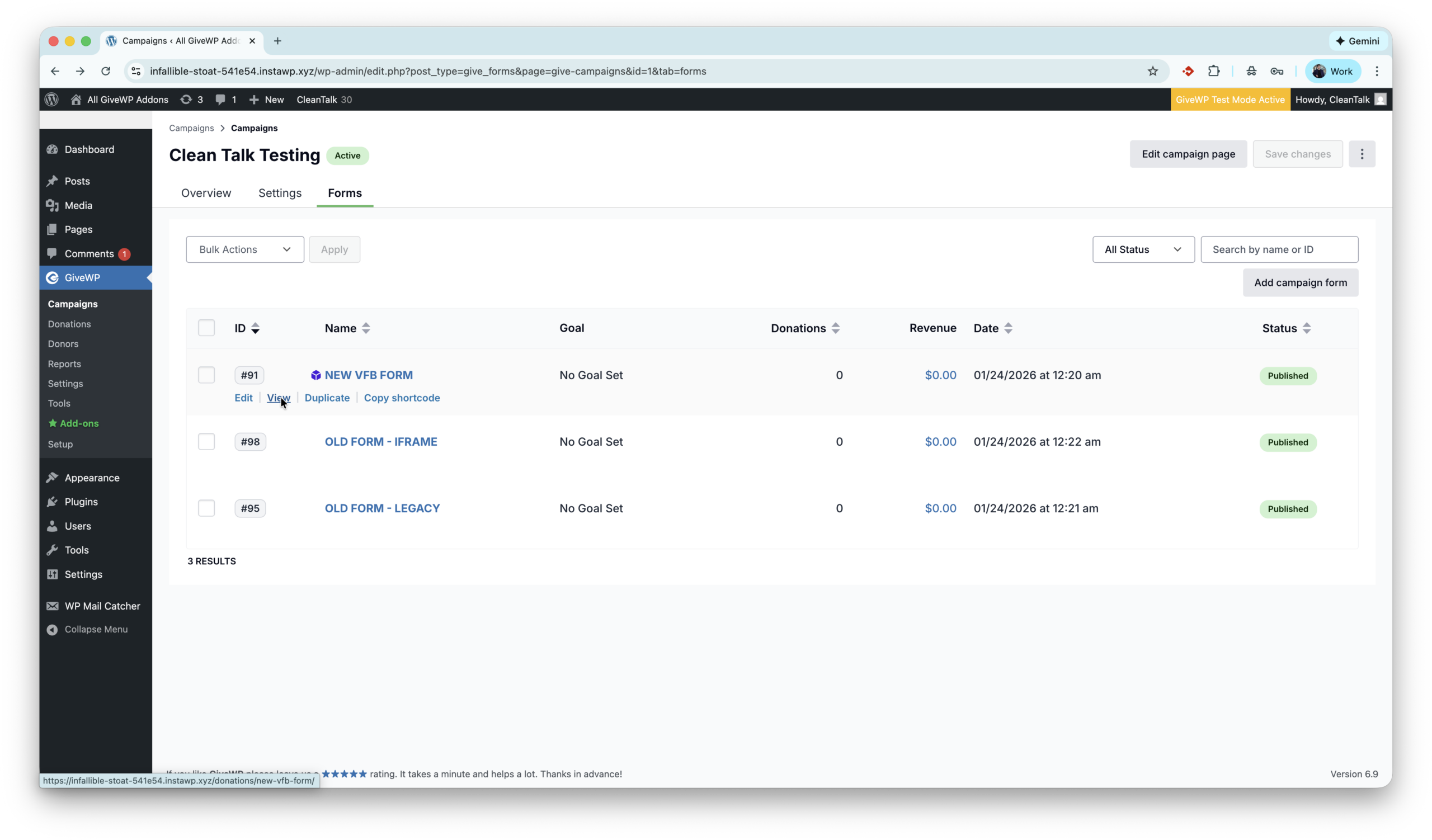
Check if spam protection works with HivePress
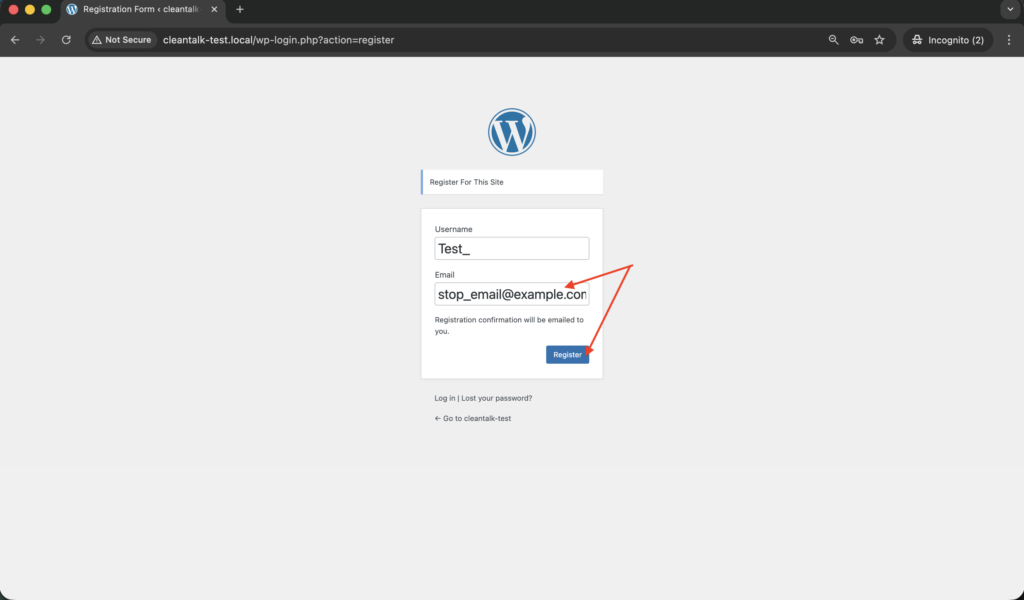
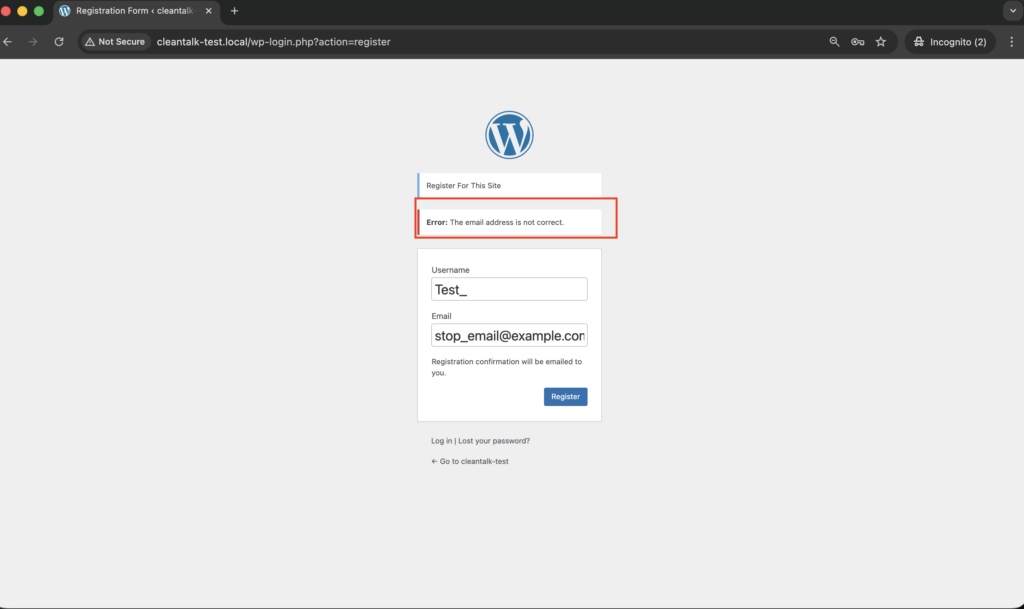
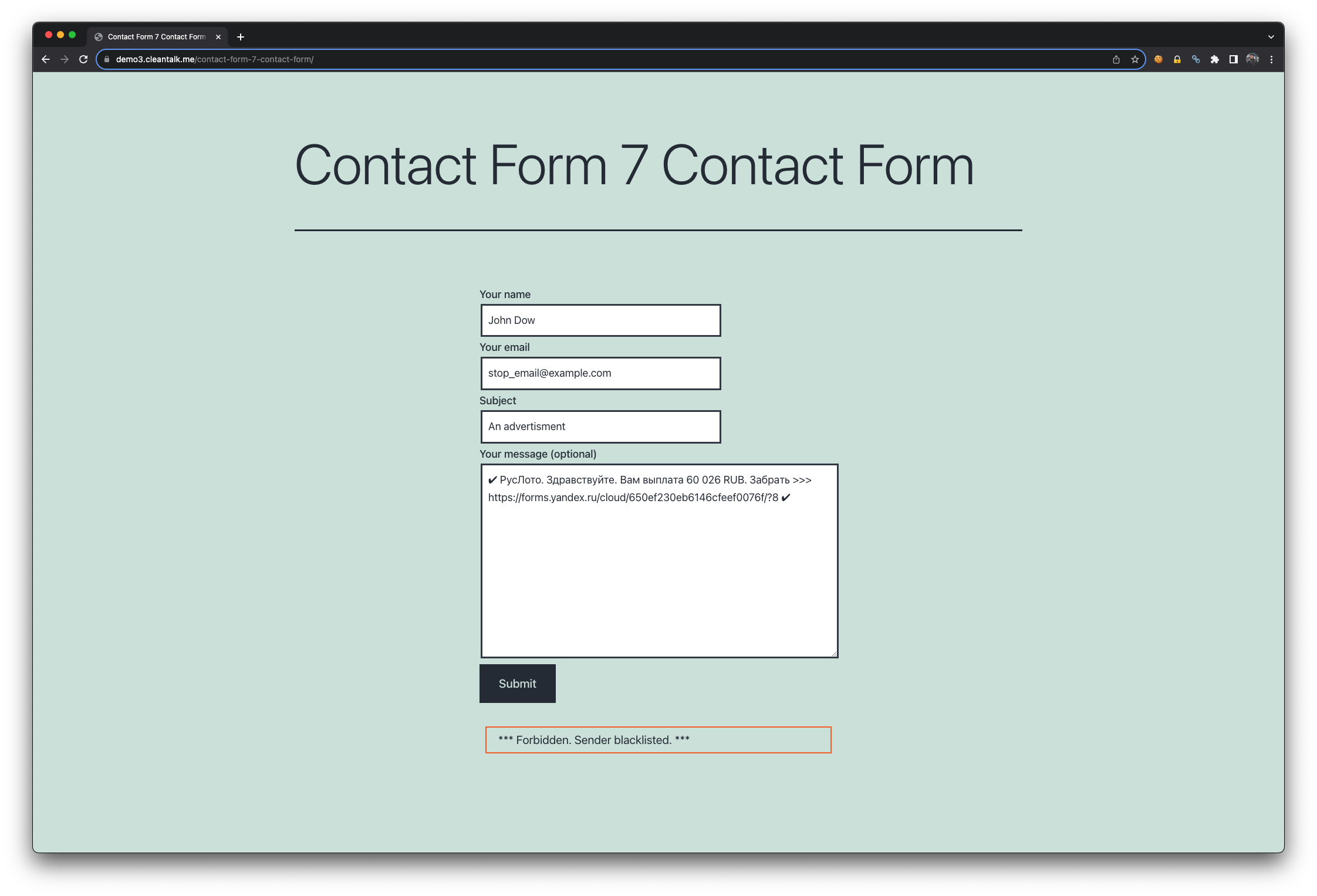
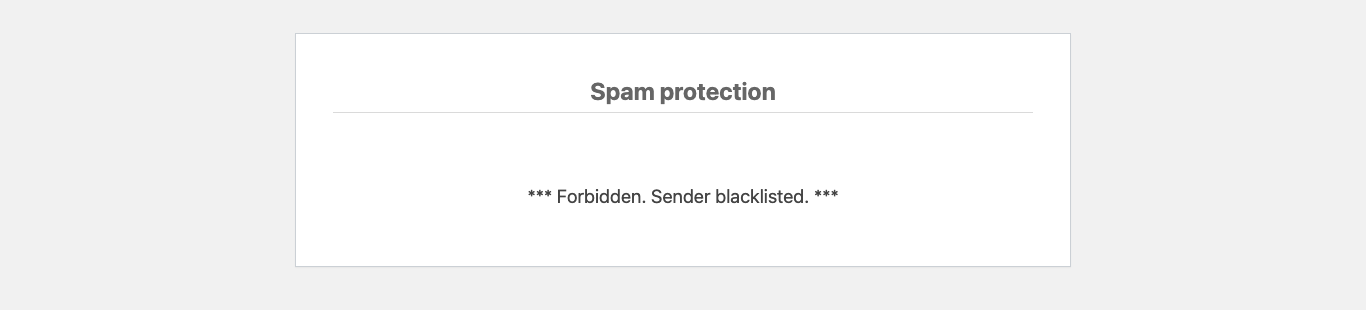
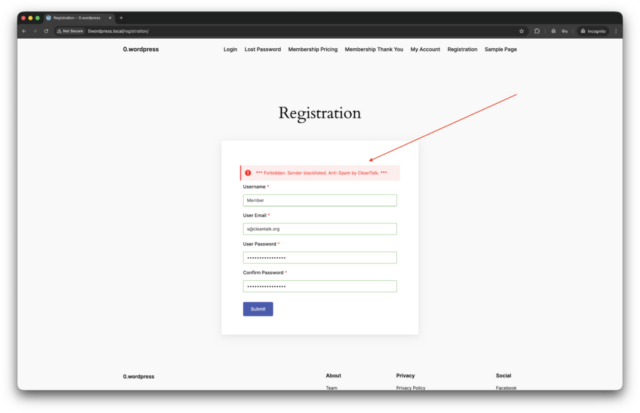
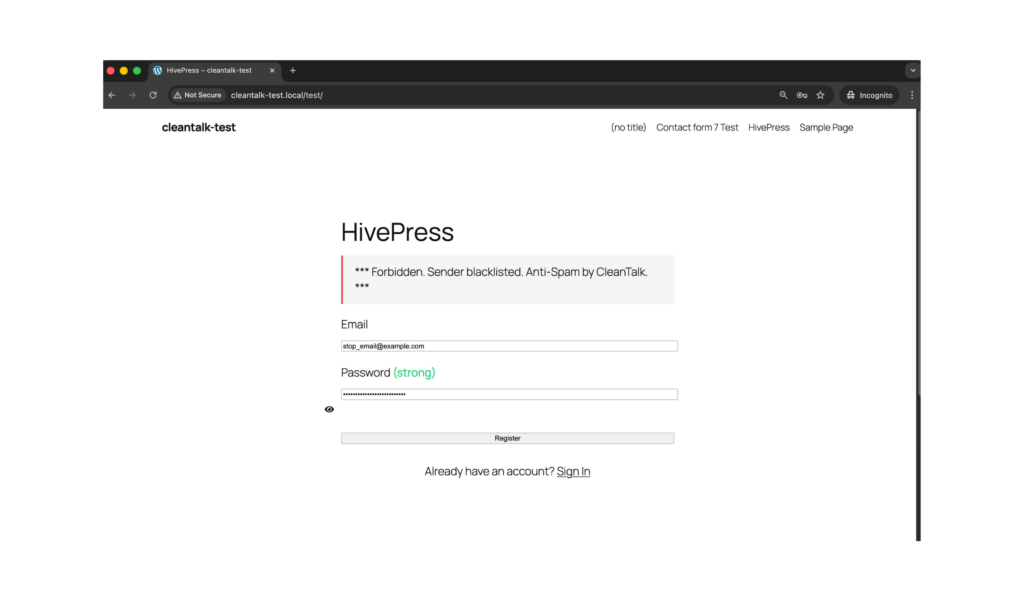
The best way to test the spam protection by using a test email,
stop_email@example.com
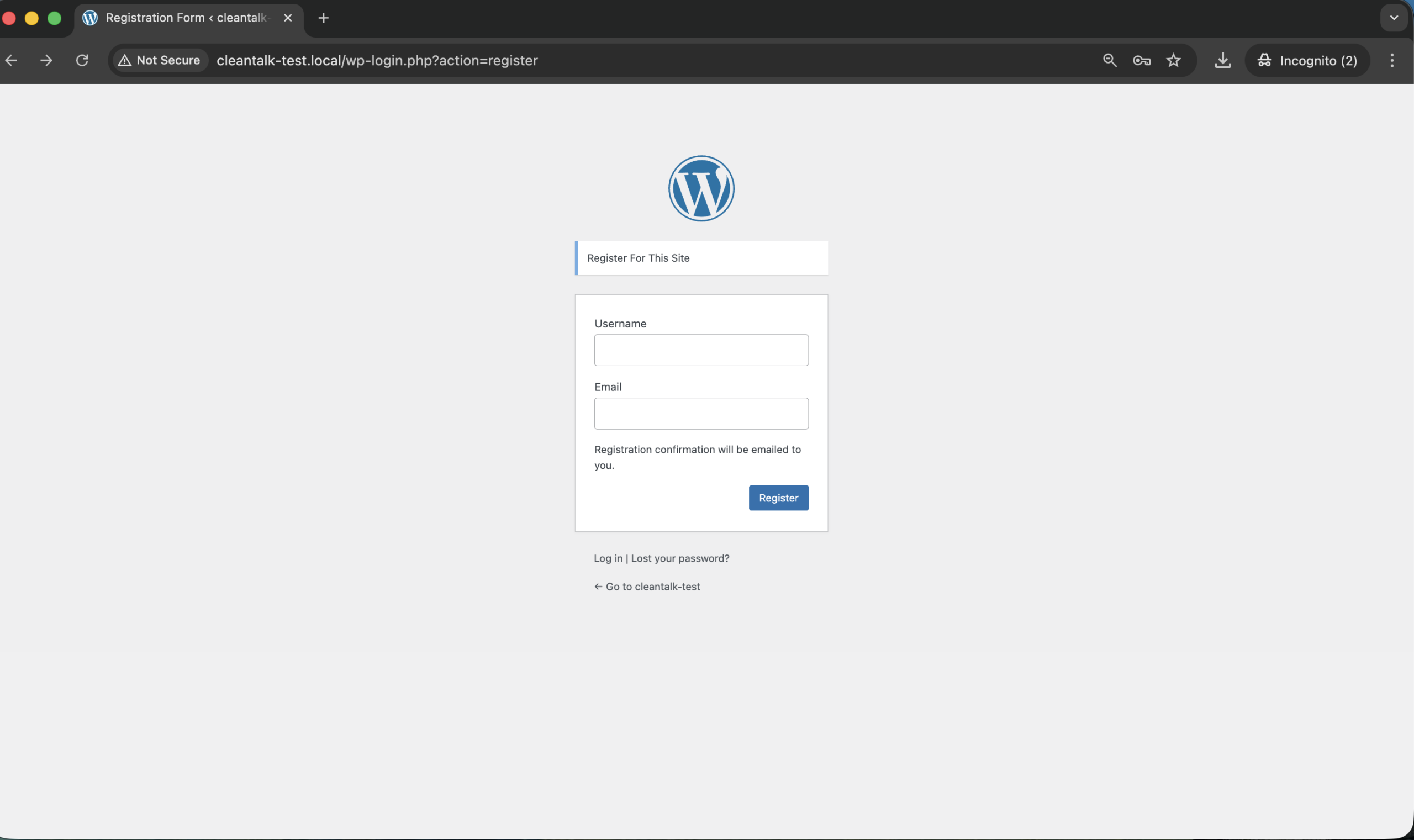
- Open page with your form (don’t forget to add the shortcode in the page content) in Incognito browser tab.
- Fill out the Contact form using stop_email@example.com as sender’s email.
- Send the form.
- You should see a message from the Anti-Spam plugin confirming that a spam submission was blocked.
*** Forbidden. Sender blacklisted. Anti-Spam by CleanTalk. ***
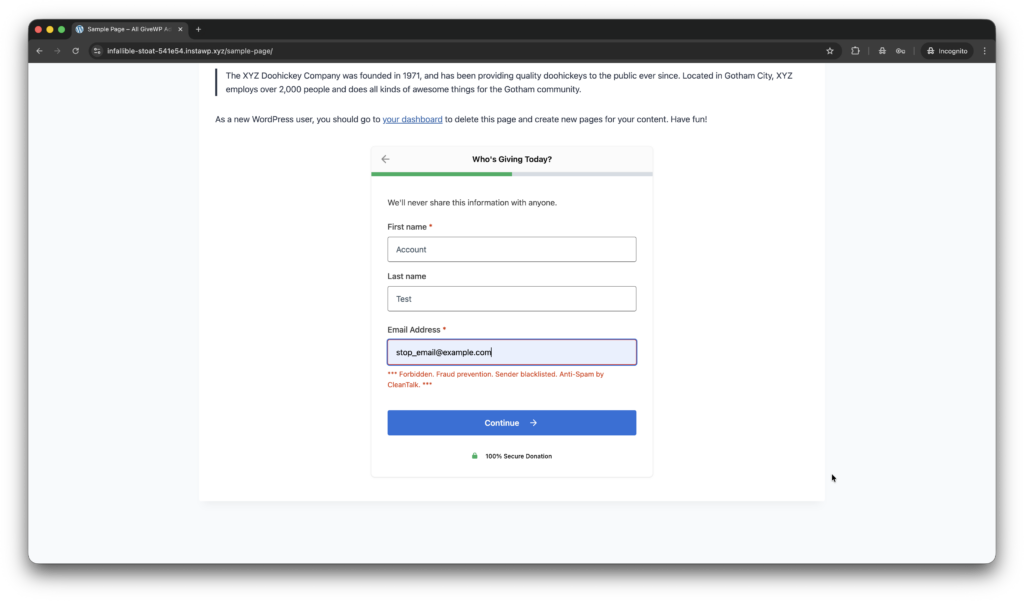
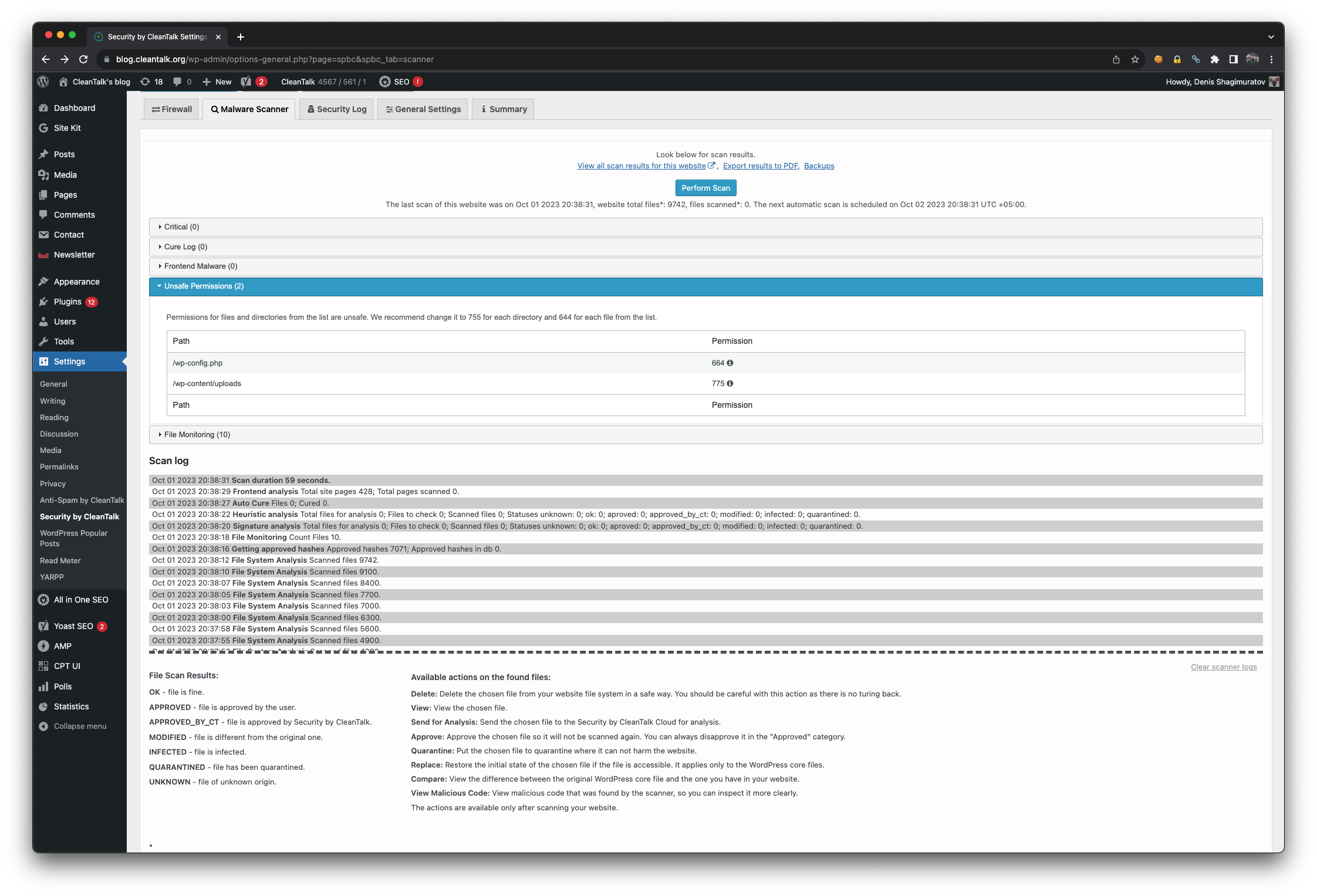
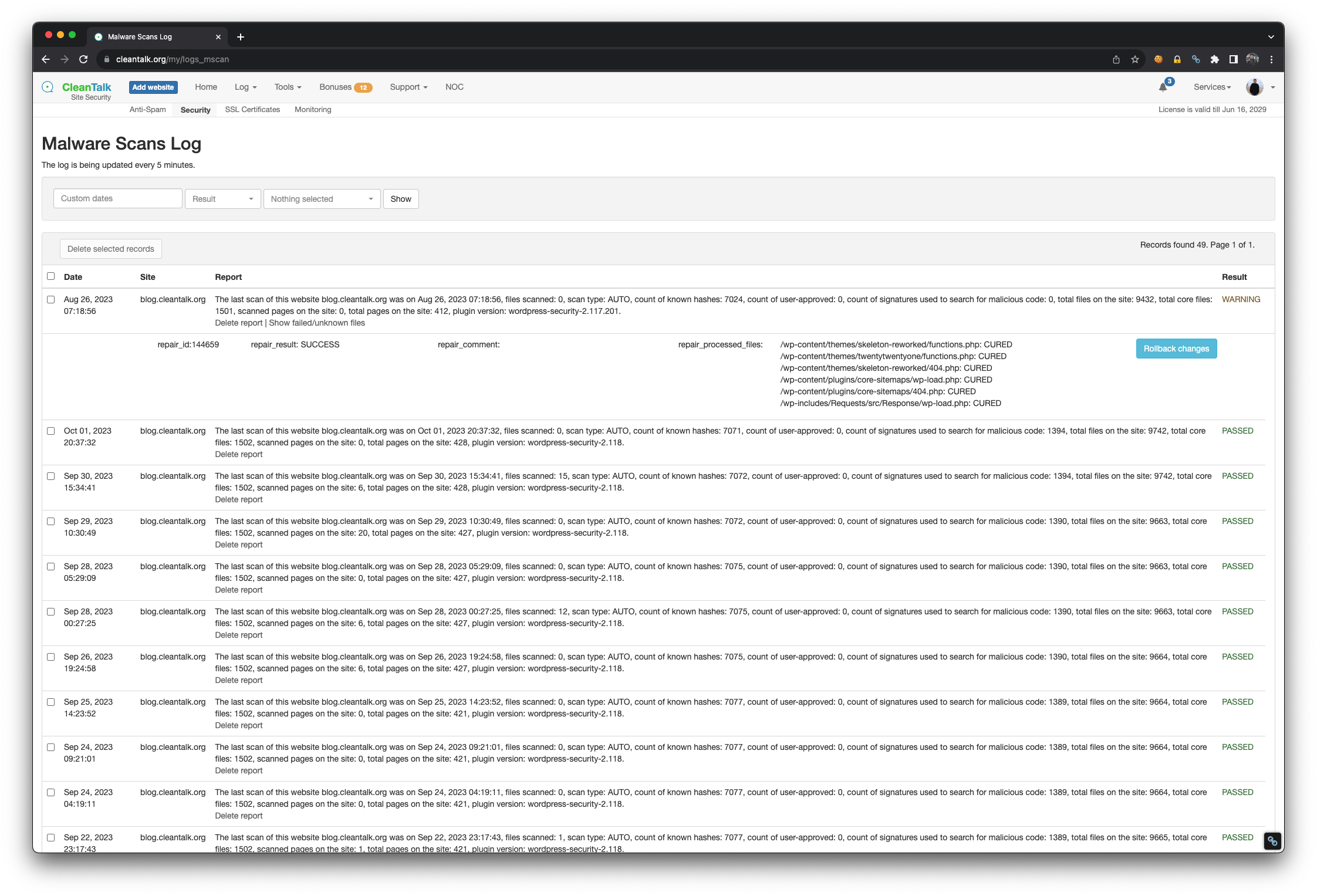
Cloud Dashboard
In addition, in the Cloud Dashboard you can find extra details regarding all submissions processed by CleanTalk, including HivePress registration and Add Listing forms:
- IP and email of the sender, as well as the sender’s activity history across other websites connected to the CleanTalk cloud.
- Geolocation of the sender.
- Date and time of the submission.
Page (URL) where the form was submitted (for example, a specific listing submission page). - Cloud decision – Approved or Denied.
- Cloud explanation for the decision (e.g. blacklisted email, bad IP reputation, spam text, etc.).
- Tools to move the sender to Block or Allow lists so you can fine-tune HivePress spam protection.
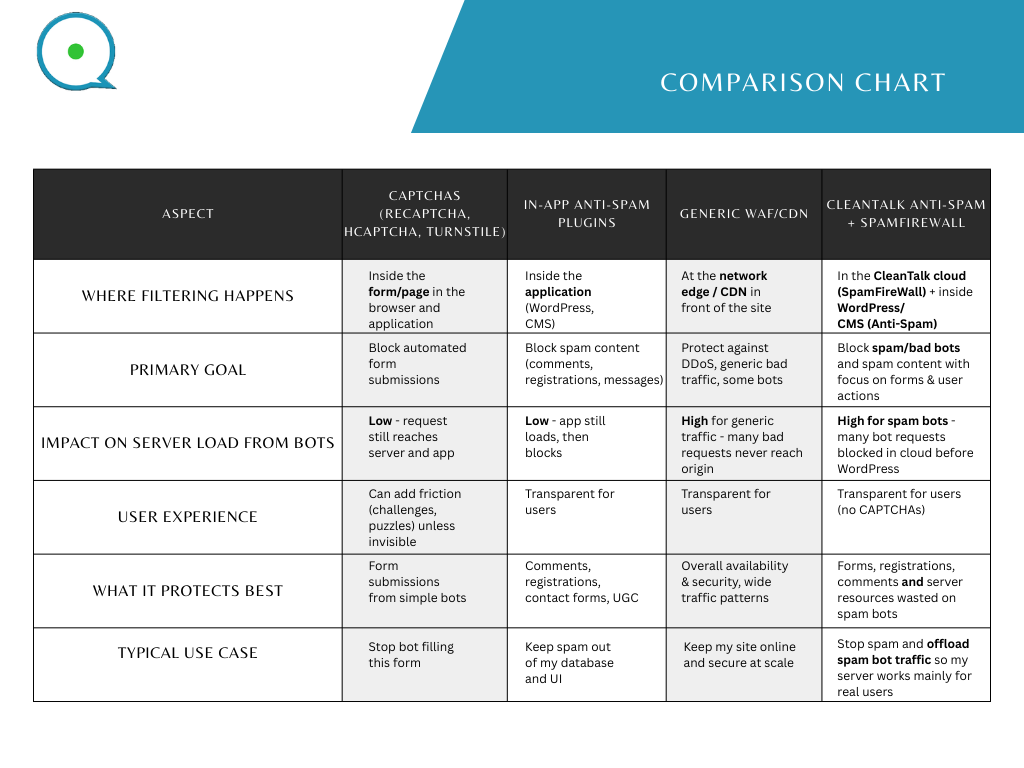
Google reCAPTCHA, hCaptcha, and Cloudflare Turnstile
Besides CleanTalk and the built-in HivePress tools, you can also use cloud CAPTCHA / anti-bot services together with HivePress to reduce spam and protect registration and Add Listing forms.
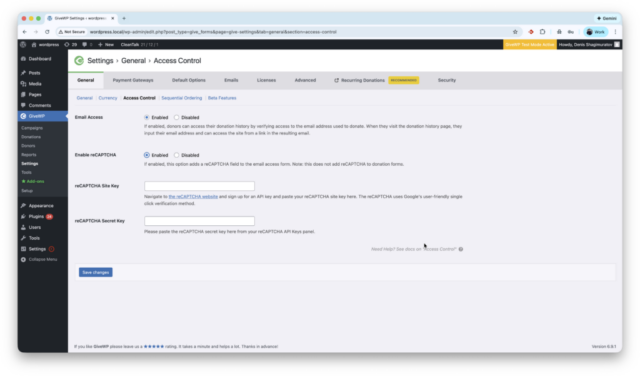
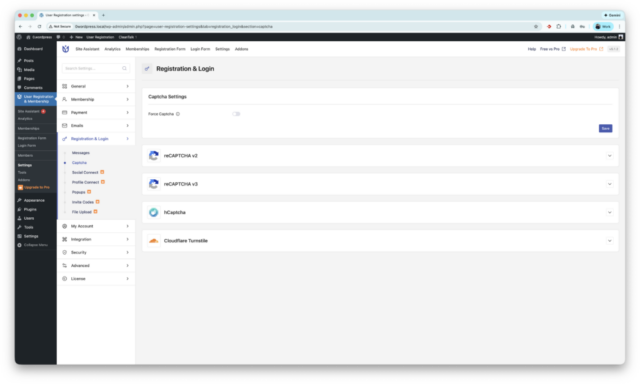
Google reCAPTCHA (native HivePress integration)
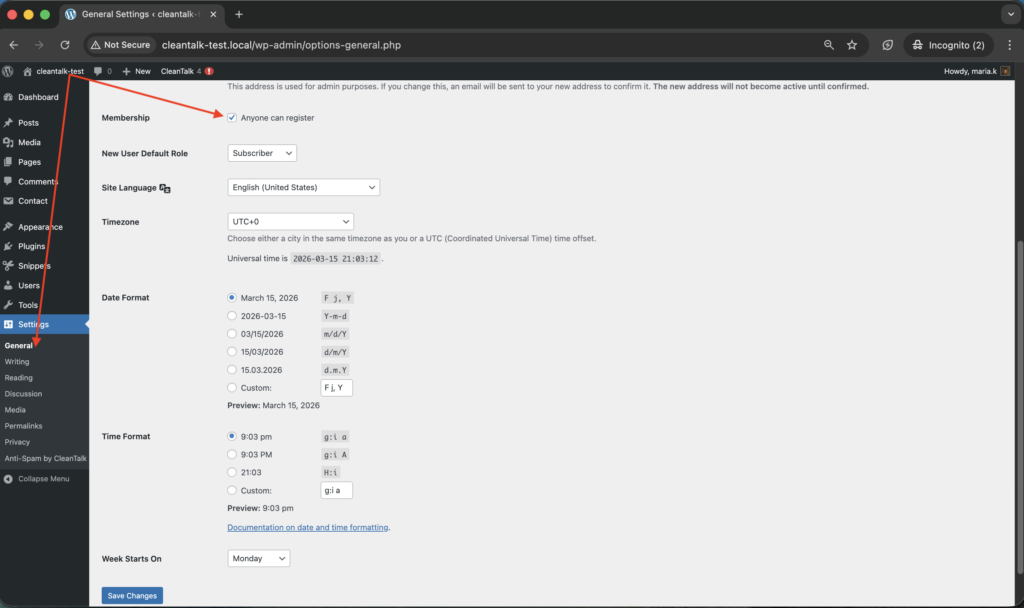
HivePress has a core integration with Google reCAPTCHA v2:
- First, register your site in the Google reCAPTCHA admin and generate a Site Key and Secret Key.
- Then go to WordPress console → HivePress → Settings → Integrations → reCAPTCHA and paste these keys.
- In the same section you can select which HivePress forms to protect (for example, registration, login, listing submission).
This helps reduce spam submissions and adds an extra security layer to HivePress forms, while CleanTalk continues to filter all submissions in the background.
hCaptcha
HivePress does not currently include native hCaptcha support. However, you can use hCaptcha on your site via separate WordPress plugins (for example, “hCaptcha for Forms and More”) that add hCaptcha to standard WordPress forms and some popular plugins.
Key benefits of hCaptcha compared to reCAPTCHA:
- Better privacy for visitors. hCaptcha collects less tracking data and is more focused on privacy and GDPR-friendly use.
- Reduced dependence on Google services. Useful for projects that prefer not to rely on Google infrastructure for branding or compliance reasons.
- Optional monetization. hCaptcha offers a program where site owners can earn small rewards for solved challenges, something reCAPTCHA does not provide.
To use hCaptcha you need to:
- obtain a Site Key and Secret Key in the hCaptcha dashboard,
- install and configure the corresponding WordPress plugin,
- and test that hCaptcha is correctly displayed and working on your HivePress registration and Add Listing forms (since there is no direct HivePress integration yet).
Cloudflare Turnstile
Cloudflare Turnstile is a modern CAPTCHA alternative that verifies users mostly in the background, without classic image puzzles.
Turnstile can be connected to WordPress via dedicated plugins that integrate Turnstile with standard WordPress forms and some third-party plugins.
Main benefits of Cloudflare Turnstile compared to classic reCAPTCHA:
- Invisible verification. Turnstile usually works silently in the background, so users can submit forms without extra clicks and image challenges.
- Higher form completion rates. With fewer interruptions, registration and listing submission forms tend to have fewer abandoned attempts.
- Strong privacy approach. Turnstile is designed to minimize user tracking and does not rely on heavy behavioral profiling, which makes it more privacy-friendly than traditional CAPTCHA solutions.
As with hCaptcha, you need to:
- obtain a Site Key and Secret Key in the Cloudflare Turnstile dashboard,
- configure the chosen WordPress plugin,
- and verify that Turnstile is actually applied to the pages where HivePress renders registration or Add Listing forms.
Honeypot, Akismet and third-party Anti-Spam plugins
Additionally, let’s consider standalone plugins and anti-spam mechanics that also work for HivePress-based websites.
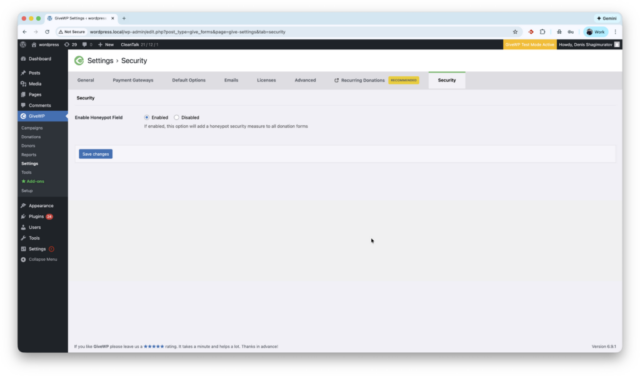
Honeypot
Honeypot is one of the simplest anti-spam mechanics against primitive spam bots. It works by adding hidden fields that are only detected and filled by bots. When a bot fills these fields, the submission is blocked automatically, while legitimate users never see any additional challenges.
Because no CAPTCHA or interaction is required, honeypots:
- help maintain a smooth user experience,
- reduce friction on registration and Add Listing forms,
- and add a lightweight extra layer of protection.
You can enable honeypot protection via a dedicated WordPress plugin, for example WP Armour – Honeypot Anti Spam.
Settings are available in the plugin configuration, for example:
- WordPress console -> Plugins -> Add New -> Search -> type ‘WP Armour’
- Install and Activate the plugin.
- WordPress console -> Settings -> WP Armour (or the plugin’s own menu item) -> enable honeypot protection for the forms used with HivePress (registration / Add Listing pages).
Effective on March 19th, 2026 users report that WP Armour does not protect or support HivePress. They observe spam subscriptions and accounts. Read more.
Third-party Anti-Spam plugins
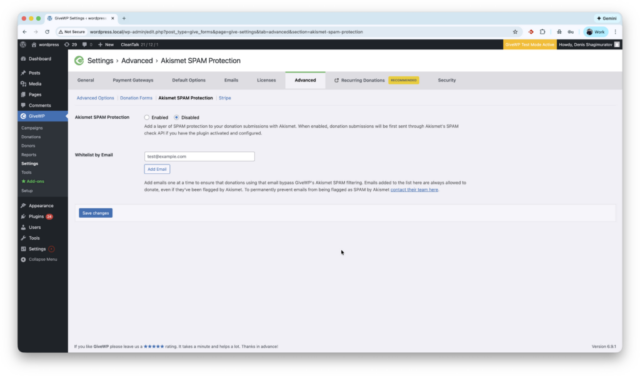
Akismet
Akismet Anti-Spam helps WordPress users automatically filter spam submissions by analyzing form data against its global spam detection network. It works in the background to identify suspicious content and prevent unwanted messages from reaching your inbox or database. This reduces manual moderation and helps keep comments and basic contact forms clean.
For HivePress websites, Akismet can be used together with CleanTalk to:
- filter blog comments and simple contact forms,
- reduce low-quality submissions outside of HivePress-specific forms.
In order to activate protection the user must:
- Install and activate the third-party plugin Akismet Anti-Spam.
- Get an API key from Akismet and enter it in the plugin settings.
- Enable spam checking for the content types you need (comments, contact forms, etc.).
Typical path:
- WordPress console -> Plugins -> Add New -> Search -> type ‘Akismet’
- Install and Activate the plugin.
- WordPress console -> Settings -> Akismet Anti-Spam -> enter API key and save.
Other universal Anti-Spam plugins
OOPSpam, Maspik, and Simple CAPTCHA Alternative are universal anti-spam plugins for WordPress that provide additional spam protection at the site level. They can help filter spam on contact forms, comments and other areas of your site that are not covered directly by HivePress integration.
All of these solutions can be found in the search results at wordpress.org:
WordPress console -> Plugins -> Add New -> Search -> type ‘WP Armour’ | ‘OOPSpam’ | ‘Maspik’ | ‘Simple CAPTCHA Alternative’
Install and Activate the chosen plugin, then configure it according to its documentation.
These third-party plugins can be used alongside CleanTalk and HivePress as optional extra layers of protection for high-risk or high-traffic projects.
This guide explains how to protect HivePress forms using the Anti-Spam plugin by CleanTalk together with additional tools such as Google reCAPTCHA, hCaptcha, Cloudflare Turnstile, honeypot mechanisms and third-party anti-spam plugins like Akismet, OOPSpam and Maspik.
Frequently Asked Questions (FAQ)
Still getting spam through your HivePress forms?
If nothing works in this guide, try a few more things:
- Block spammers by particular IPs, countries and email masks via Personal lists in your CleanTalk account.
- Enable listing moderation in HivePress, so new listings must be approved by an admin before they go live.
- Check for plugin conflicts – temporarily disable other anti-spam / security plugins and test HivePress registration and Add Listing forms only with CleanTalk enabled.
- Submit a support request to CleanTalk, attaching examples of spam submissions (IPs, emails, message text, page URLs). The support team will do their best to tune spam protection for your specific case.
reCAPTCHA not saving in HivePs settingress or showing errors
If reCAPTCHA keys are not saved or you see an error in HivePress → Settings → Integrations → reCAPTCHA:
- Make sure you are using the correct key type (usually reCAPTCHA v2 for HivePress).
- Double-check that the domain in the Google reCAPTCHA admin exactly matches your site.
- Remove any extra spaces when pasting the Site Key and Secret Key.
- Try temporarily disabling other CAPTCHA / security plugins and saving the settings again.
- If the issue persists, you can switch to an alternative solution such as hCaptcha or Cloudflare Turnstile via a separate WordPress plugin, while keeping CleanTalk as your main spam filter.
HivePress + hCaptcha / Turnstile does not prevent spam
If you enabled hCaptcha or Cloudflare Turnstile but spam still comes through:
- Do not rely on hCaptcha / Turnstile alone – always keep CleanTalk Anti-Spam enabled as the primary filter.
- Enable honeypot protection if it is available in your chosen security / form plugins to catch simple bots.
Check that there are no plugin conflicts disabling CleanTalk checks or bypassing them. - Use layered protection: CleanTalk + CAPTCHA (reCAPTCHA / hCaptcha / Turnstile) + HivePress moderation usually works much better than any single method.
Emails from HivePress forms are going to spam.
- Check SMTP configuration and avoid sending mail via the default PHP mail() function.
- Install and configure an SMTP plugin, so your site sends messages through an authenticated email account (hosting mail, Gmail, or a transactional service).
- Verify that your domain has proper SPF / DKIM / DMARC records to improve sender reputation.
- After configuring SMTP, send a few test submissions from HivePress forms and confirm that notifications now arrive in the inbox, not in spam.
Recommended Anti-Spam Stack for HivePress (2026)
Finally, no single anti-spam tool can stop every type of spam submission. The most reliable approach for HivePress websites is a layered protection stack, where each tool blocks a different category of bots and spam behavior.
Starting from the latest plugin update, the Anti-Spam plugin by CleanTalk includes a direct integration with HivePress. It automatically protects the HivePress registration form and the Add Listing form before a new user account or listing is created, without any extra settings inside HivePress. This integration is the core of the recommended anti-spam stack below.
Recommended setup by site type
Small business directory / local listings
- CleanTalk Anti-Spam (with direct HivePress integration)
- Optional honeypot protection in a security/form plugin
- Basic HivePress listing moderation
High-traffic classifieds or service marketplace
- CleanTalk Anti-Spam (with direct HivePress integration)
- Google reCAPTCHA or Cloudflare Turnstile on registration and Add Listing forms
- Listing moderation for new or untrusted users
Membership / registration-heavy HivePress sites
- CleanTalk Anti-Spam (with direct HivePress integration)
- Cloudflare Turnstile or hCaptcha on registration and login
- Optional honeypot protection for additional bot filtering
By now, most spam issues in your HivePress registration, login and Add Listing forms should be resolved. If not, sign up for a CleanTalk account or log in to your existing one and contact our support team – we will be happy to help you fine-tune spam protection for your specific case.