-
How to Reduce Server Load by Simply Filtering Bad Traffic
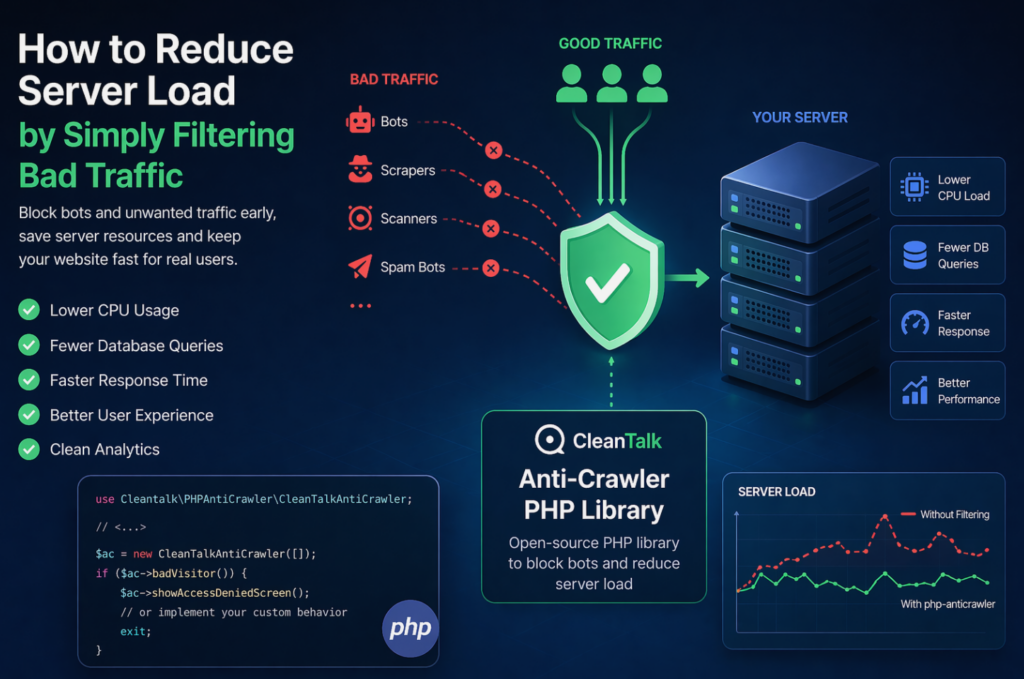
When a website starts slowing down, many teams immediately think about scaling infrastructure: adding CPU, RAM, more servers, or optimizing the database. In reality, a significant part of server load is often caused not by real users, but by automated traffic — bots, scrapers, vulnerability scanners, spam robots, and aggressive crawlers. These requests may continuously
FEEDBACK LOG
The Latest
-
Fraud Prevention: How CleanTalk Can Help Identify and Prevent Fraud Attacks
Fraud attacks have become increasingly prevalent, posing a serious threat to businesses and individuals alike. These attacks involve the use of deceptive tactics to gain unauthorized access to sensitive information or financial resources. Fraudsters often utilize various means such as phishing, identity theft, and credit card fraud to carry out their malicious activities. The consequences…
-
Brevo Forms (formely Sendinblue) – Spam Protection for WordPress
CleanTalk added spam protection for Brevo Forms using direct form integration. So in case, you prefer using Brevo Forms be sure to use the most effective Anti-Spam plugin. Read the guide below and learn 4 steps to protect your Brevo Forms from spam. Once the CleanTalk Anti-Spam plugin is installed it starts to protect all…
-
Protect Elementor Forms from spam
While using Elementor Contact Form, always be sure to use the most effective Anti-Spam plugin. Read the guide below and learn how to protect your Elementor Contact Form from spam in 5 minutes. Once CleanTalk Anti-Spam plugin is installed it starts to protect all of the existing forms on your WordPress website. It may not…
-
AWeber Forms – Spam Protection for WordPress
CleanTalk added spam protection for Aweber Forms using direct form integration. So in case, if you prefer using Aweber Forms be sure to use the most effective Anti-Spam plugin. Read the guide below and learn 4 steps to protect your Aweber Forms from spam. Once the CleanTalk Anti-Spam plugin is installed it starts to protect…



