-
7 Ways to Prevent Fake Registrations on WordPress (with CleanTalk)
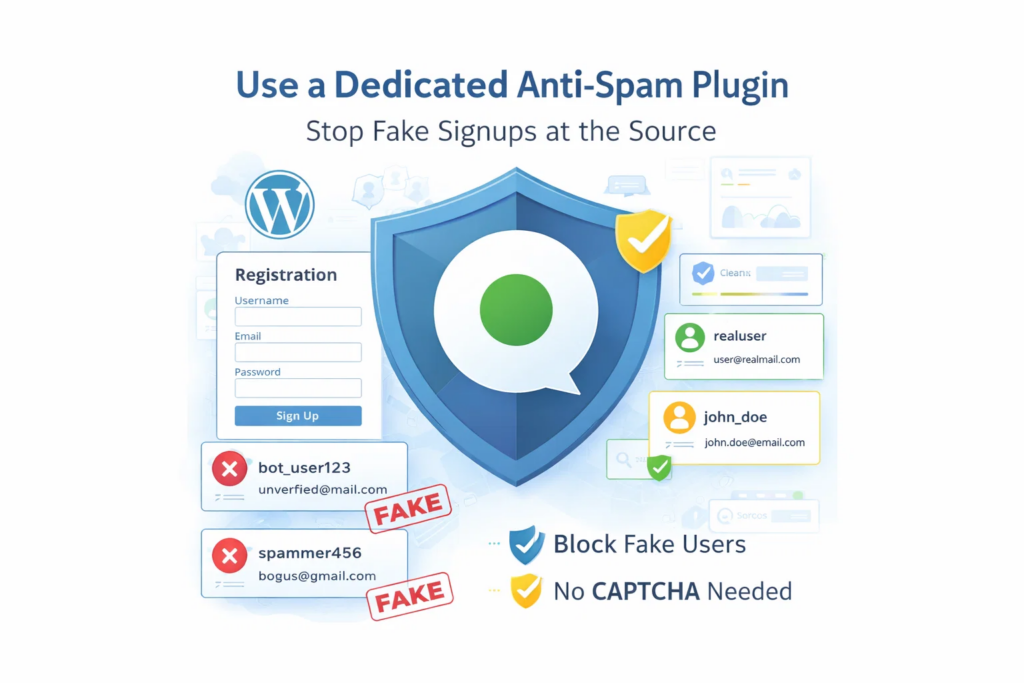
Fake registrations are more than a minor admin inconvenience. They fill your database with junk accounts, waste moderation time, reduce signup quality, and make it harder to understand what real user activity looks like. For WordPress sites, this problem is especially common. Registration forms are public by design, which makes them an easy target for
FEEDBACK LOG
The Latest
-
Plugin Security Certification: “Simple Author Box” Version 6.3.1: Security at the Forefront
·
In the world of WordPress, there are hundreds of thousands of plugins, and security plays a crucial role in ensuring the smooth operation of your website. In this article, we present an overview of the “Simple Author Box” plugin version 6.3.1 and some exciting news: it has undergone rigorous security testing and has earned the…
-
CVE-2023-4827 – File Manager Pro < 1.8 - Remote Code Execution via CSRF
During testing of the plugin, a CSRF vulnerability was discovered in action=rename, which can lead to denial of service and theft of the password from the database, thereby allowing an attacker to get inside the web application and gain a foothold in it. Replace any data in the database and do everything that an administrator…
-
CVE-2023-3664 – FileOrganizer <= 1.0.2 - Admin+ Arbitrary File Access
During a security assessment of the FileOrganizer plugin, a medium vulnerability was uncovered in versions up to and including 1.0.2. This vulnerability allows an attacker to manipulate the plugin’s root folder, potentially compromising the security of the entire system. The plugin does not restrict functionality on multisite instances, allowing site admins to gain full control…
-
CVE-2023-4238 – Prevent files / folders access < 2.5.2 - Remote Code Execution
A severe security loophole has come to light in the Prevent files / folders access plugin, triggering concerns over the safety of WordPress websites. This vulnerability, tracked as CVE-2023-4238, opens the door to remote code execution through file uploads. Our testing revealed a startling scenario: an attacker can potentially upload a PHP file to the…

