If you use Asgaros Forum on a WordPress website, spam will eventually become a real problem. Fake registrations, bot topics, junk replies, and low-quality forum activity can quickly damage the quality of discussions and create extra work for moderators.
This guide explains how to set up Asgaros Forum spam protection using CleanTalk as the main filtering layer on your website, together with additional tools such as guest-post restrictions, approval and banning features, third-party CAPTCHA integrations, and tighter forum permissions. Asgaros Forum describes itself on WordPress.org as a lightweight, feature-rich WordPress forum plugin. Its documented feature set includes profiles, guest postings, approval, banning, reporting, moderators, permissions, and usergroups.
This protection approach can be applied to forum registrations, guest posts, new topics, replies, and other public-facing actions inside Asgaros Forum.

Asgaros Forum for WordPress
First, it helps to understand what Asgaros Forum is and why spam protection matters here.
Asgaros Forum is a WordPress plugin that adds a discussion board to a WordPress site. According to its WordPress.org page, it is designed as a lightweight and feature-rich forum solution. The plugin page also notes that it can automatically create a forum page during installation, or you can insert a forum manually with the [forum] shortcode.
In practice, Asgaros Forum can help website owners:
- build a WordPress-based discussion board
- allow users to create topics and replies
- support member profiles and forum communities
- manage moderation, bans, permissions, and reports
That flexibility is exactly why spam becomes an issue. Once a forum is public, it can attract bots, fake accounts, low-quality replies, and unwanted promotional activity.
As WordPress.org shows, Asgaros Forum is currently used on over 10,000 websites. Its official plugin page describes it as a lightweight and feature-rich forum plugin for WordPress with features such as guest postings, approval, banning, reporting, moderators, permissions, and usergroups.
Plugin Homepage at WordPress.org | FAQ and support details at WordPress.org.
Why Asgaros Forum Attracts Spam
A public forum naturally creates more spam entry points than a simple contact form.
In real-world use, the most common problems usually include:
- spam registrations
- bot-created topics
- junk replies with irrelevant links
- low-quality posts from guests or throwaway accounts
This is especially important for forums because spam does not just create clutter. It can damage trust, bury useful discussions, and increase the amount of work needed from moderators and administrators.
Because Asgaros Forum can allow guest postings and public participation, spam risk is often higher than on a members-only discussion board. If guests can post freely, forum owners should treat permissions, moderation, and anti-spam filtering as part of the same setup rather than as separate tasks.
Anti-Spam by CleanTalk
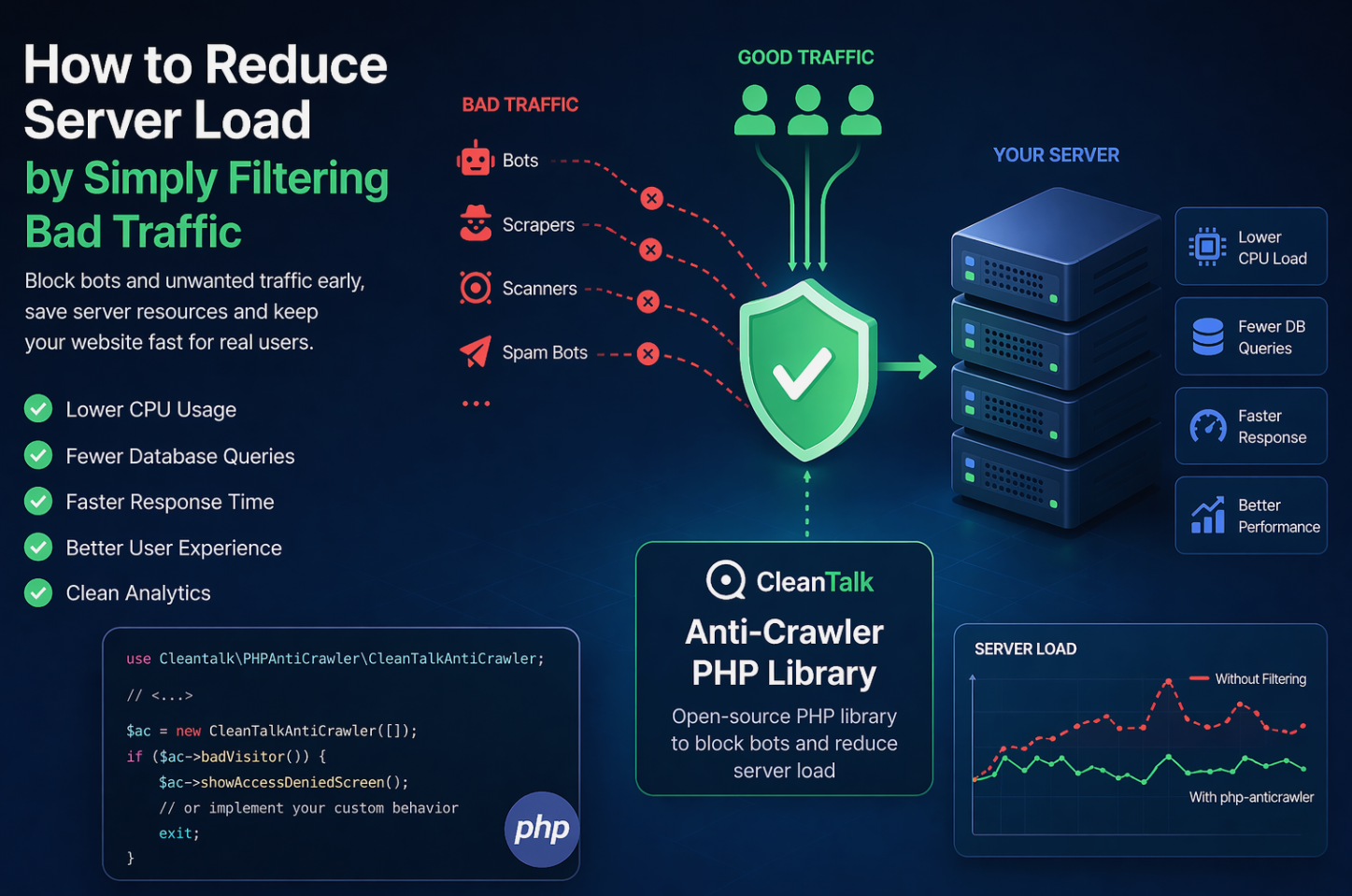
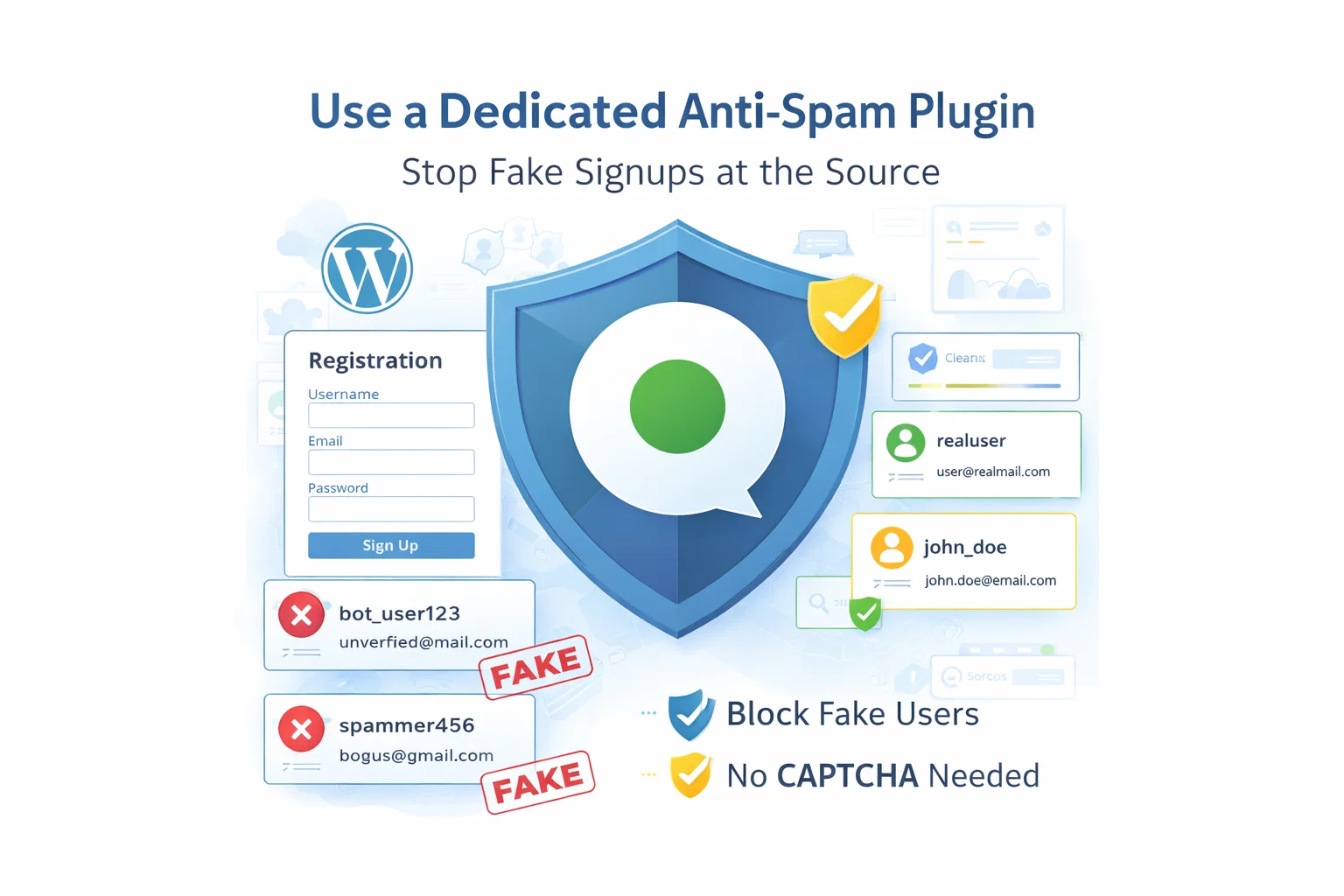
The main tool we’re going to use here is CleanTalk Anti-Spam.
CleanTalk is a cloud-based anti-spam service for WordPress sites. Its official WordPress plugin page describes it as CAPTCHA-free spam protection for forms, comments, registrations, subscriptions, and many other submission types. The current WordPress.org listing shows more than 200,000 active installations.
In practical terms, CleanTalk helps by:
- filtering suspicious registrations before they become real accounts
- checking sender reputation and email quality
- detecting automated and repeated abuse patterns
- reducing junk posts before they become part of forum activity
That matters because the real cost of forum spam is not only visual clutter. It also means lower discussion quality, more moderation work, and a weaker community experience.
According to WordPress.org, Anti-Spam by CleanTalk for WordPress has over 200,000 active installations, with 3,168 reviews and an average rating of 4.8.
Plugin Homepage at cleantalk.org | Latest release at GitHub.com
Install the CleanTalk Anti-Spam plugin
Show Instructions
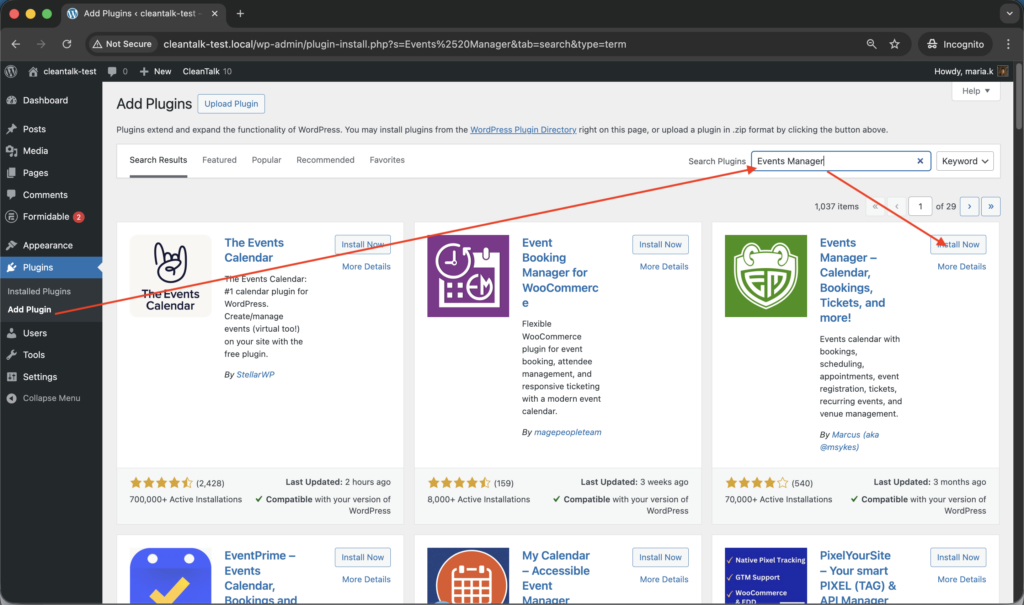
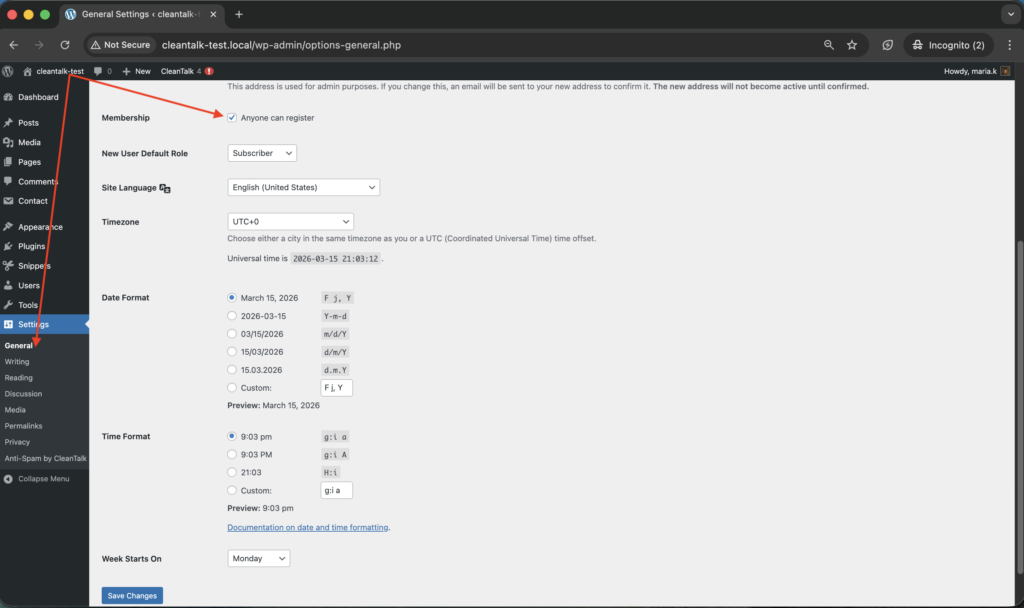
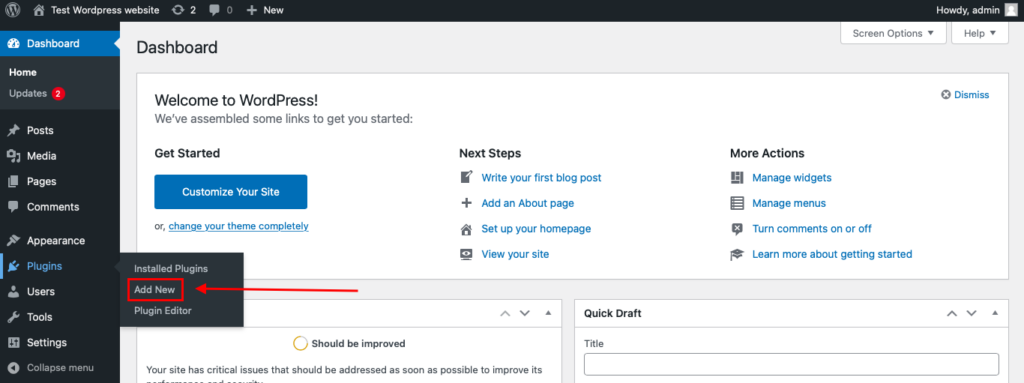
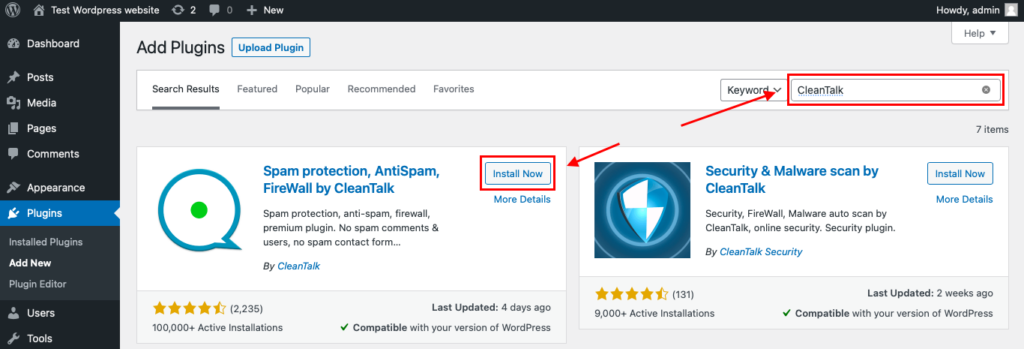
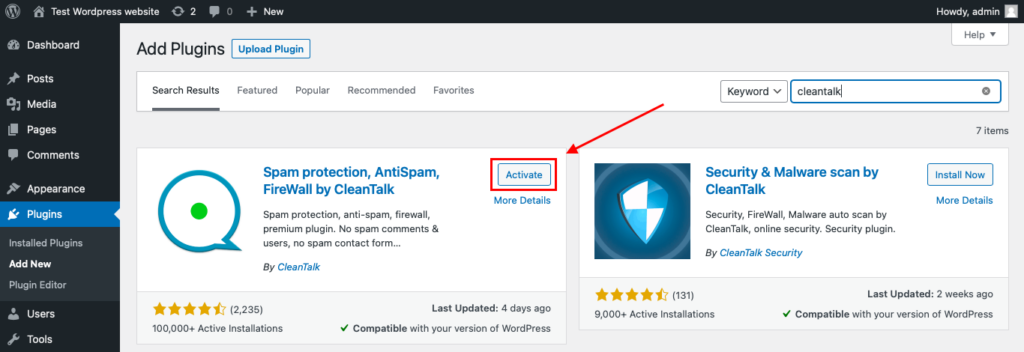
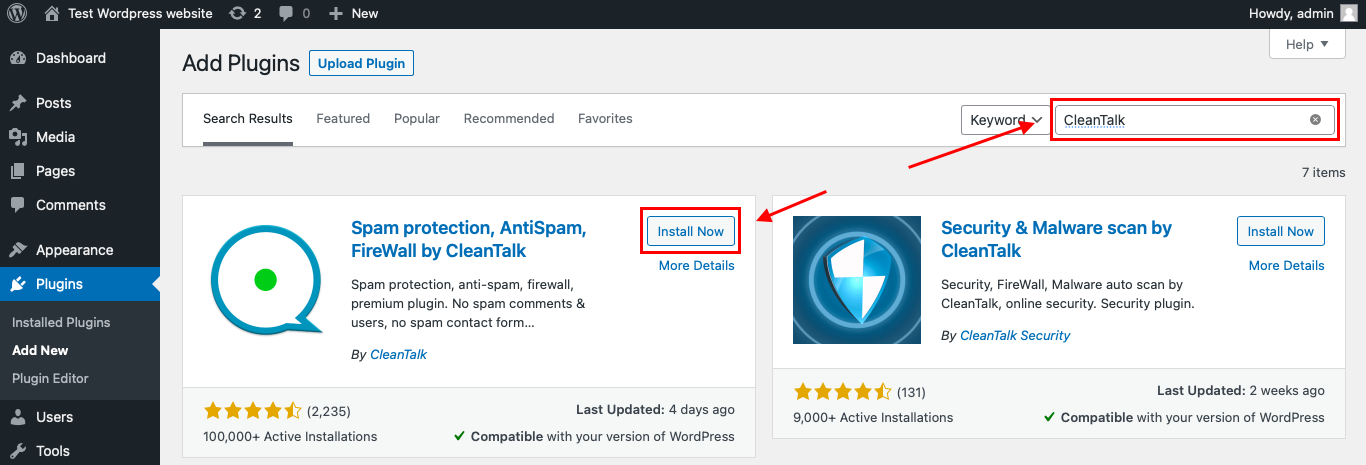
To install the Anti-Spam plugin, go to your WordPress admin panel → Plugins → Add New.
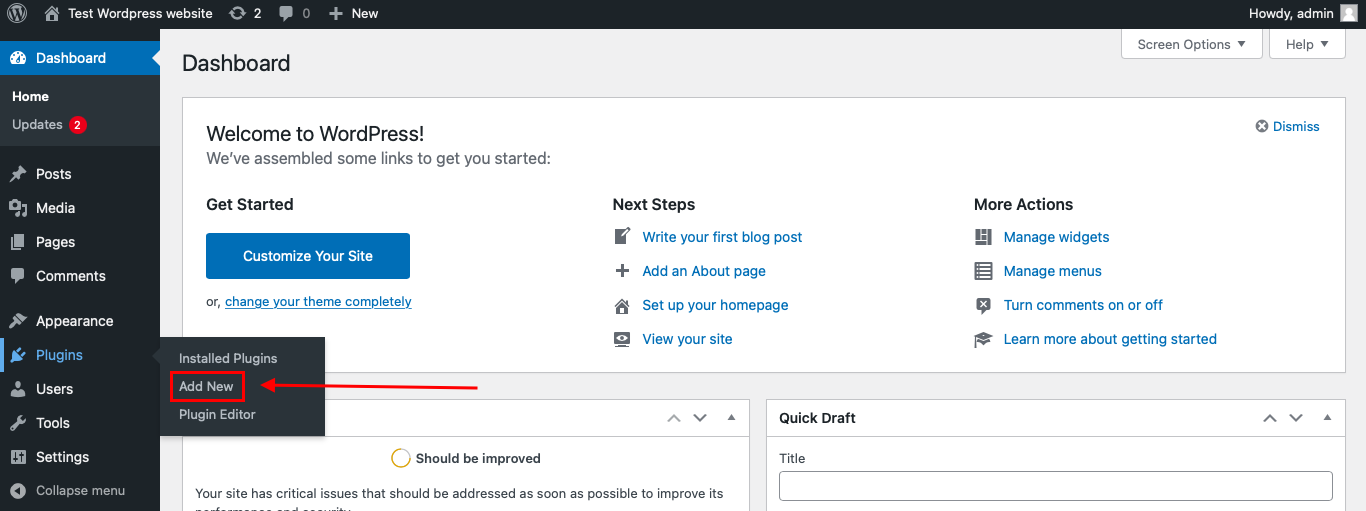
Then enter «СleanTalk» in the search box and click the Install button for «Spam protection, Anti-Spam, FireWall by CleanTalk».
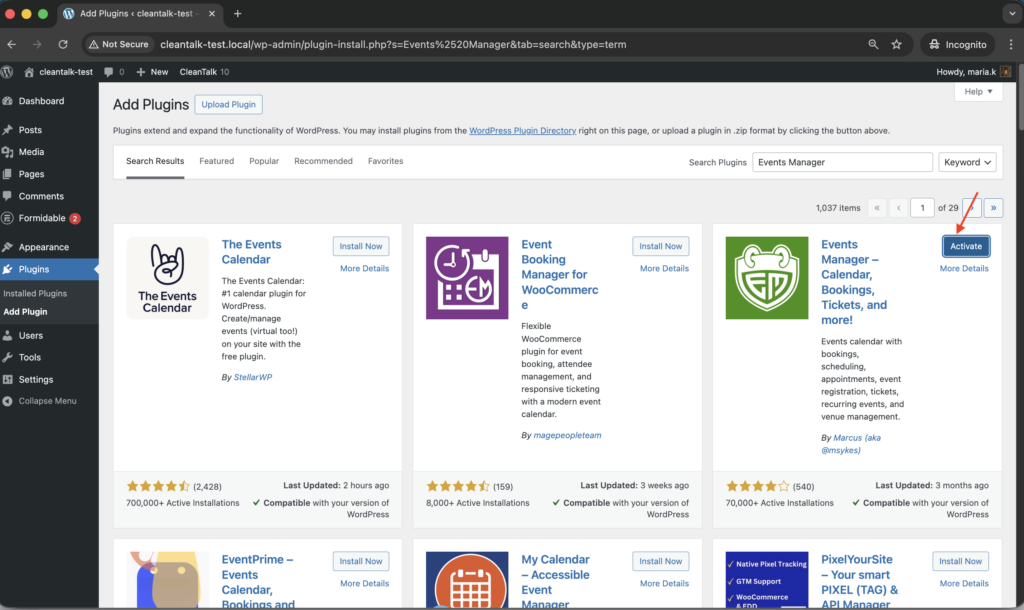
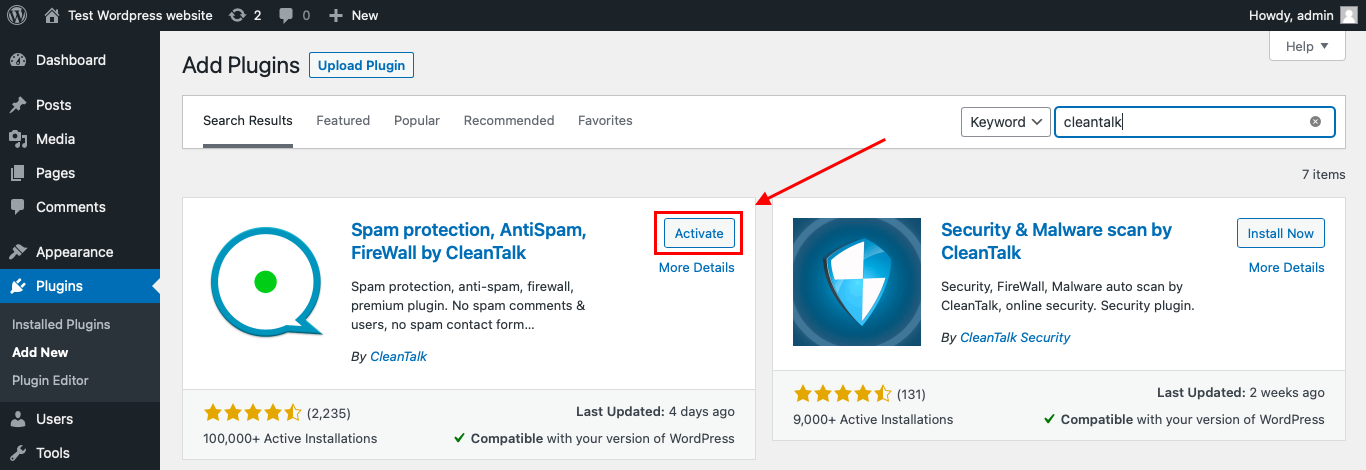
After installing the plugin, click the «Activate» button.
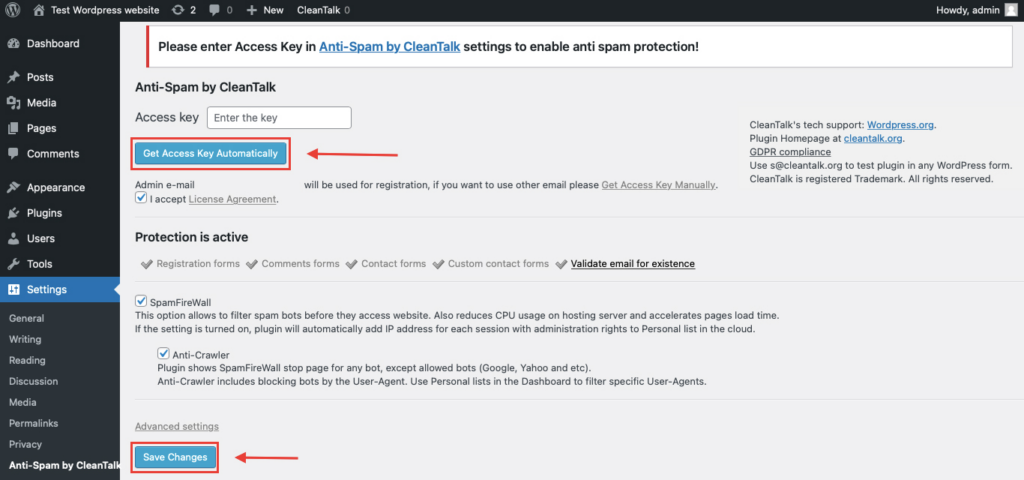
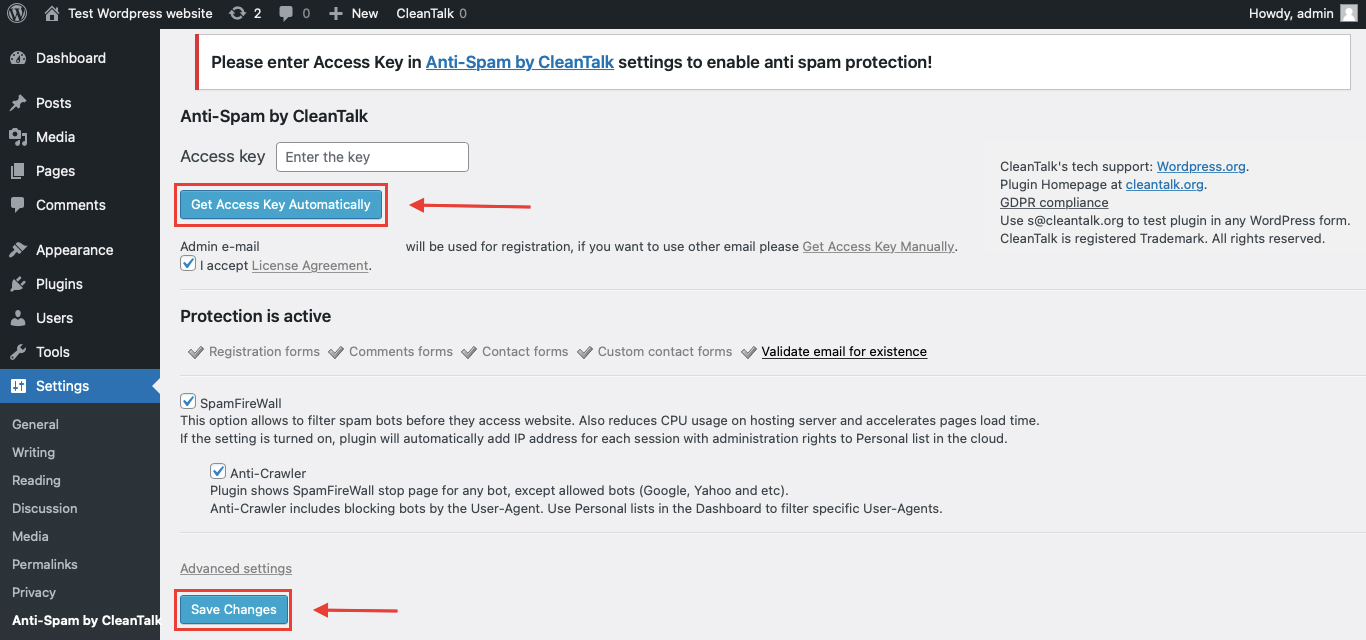
After it is done go to the plugin settings and click the «Get Access Key Automatically» button. Then just click the «Save Settings» button.
That’s it! From now you know how to completely protect your HivePress from spam.
Once that is done, your website has a background anti-spam layer that can help reduce suspicious forum activity before unwanted registrations or posts reach the live forum.
How CleanTalk Fits into the Asgaros Forum Workflow
Asgaros Forum runs inside WordPress, so the most effective place to apply protection is before spam becomes a normal part of the community workflow.
That means the focus should not be only on visible forum pages. The more important point is what happens when a user registers, posts as a guest, creates a topic, or submits a reply.
If a site uses Asgaros Forum for community discussions, a site-level anti-spam layer can help stop suspicious activity before it becomes a normal topic, reply, or registration.
If the forum uses extra integrations, custom workflows, or manual moderation rules, the filtering layer should still be placed before the submission is accepted as normal forum content.
That is the key principle: do not wait until spam is already visible inside the forum. Stop it earlier in the process.
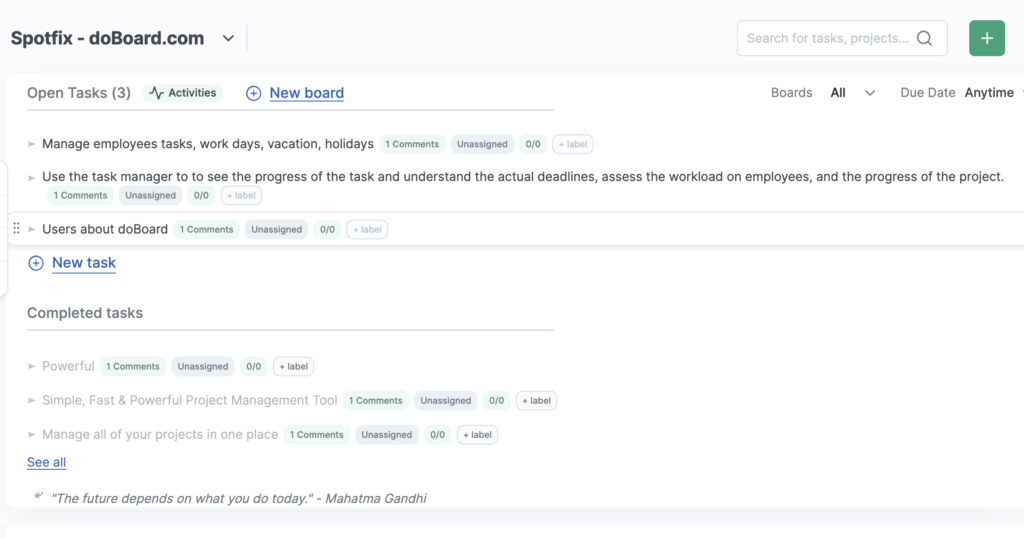
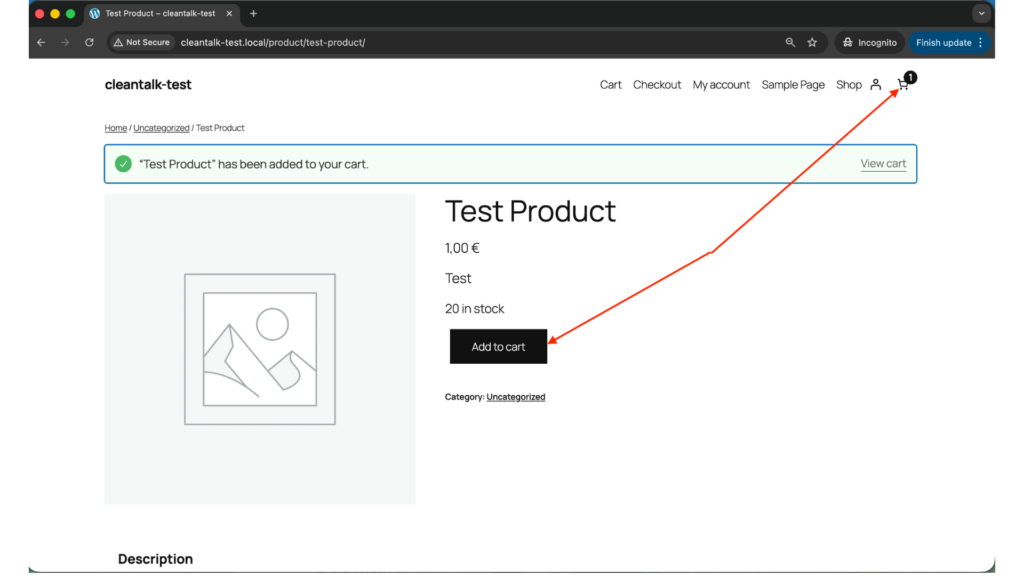
How to Check Whether Spam Protection Works
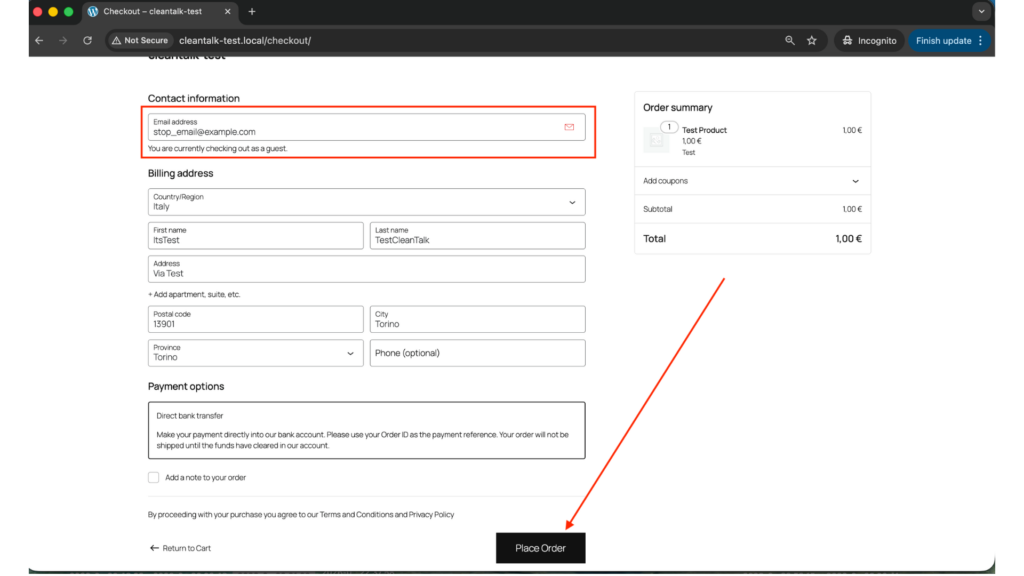
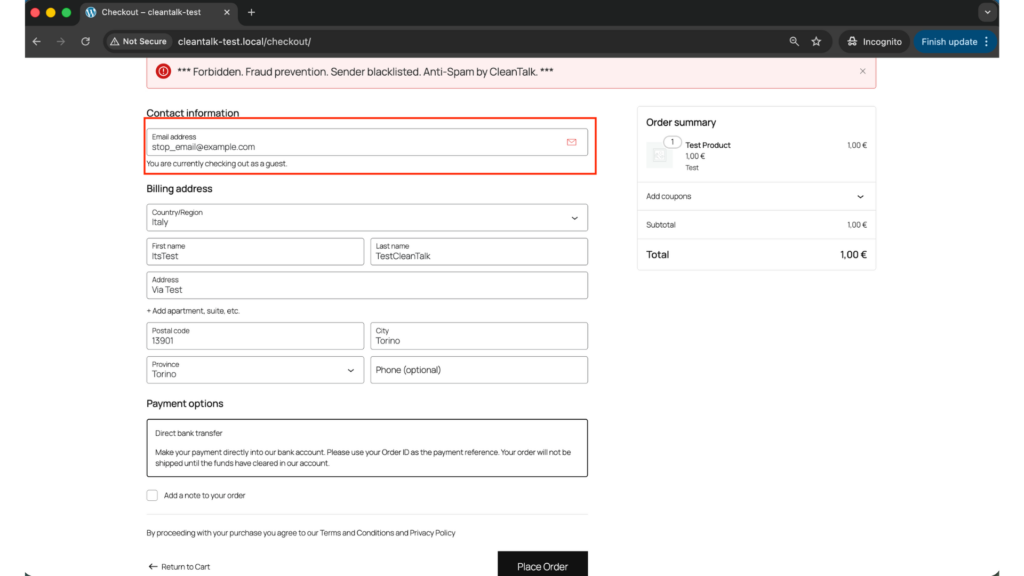
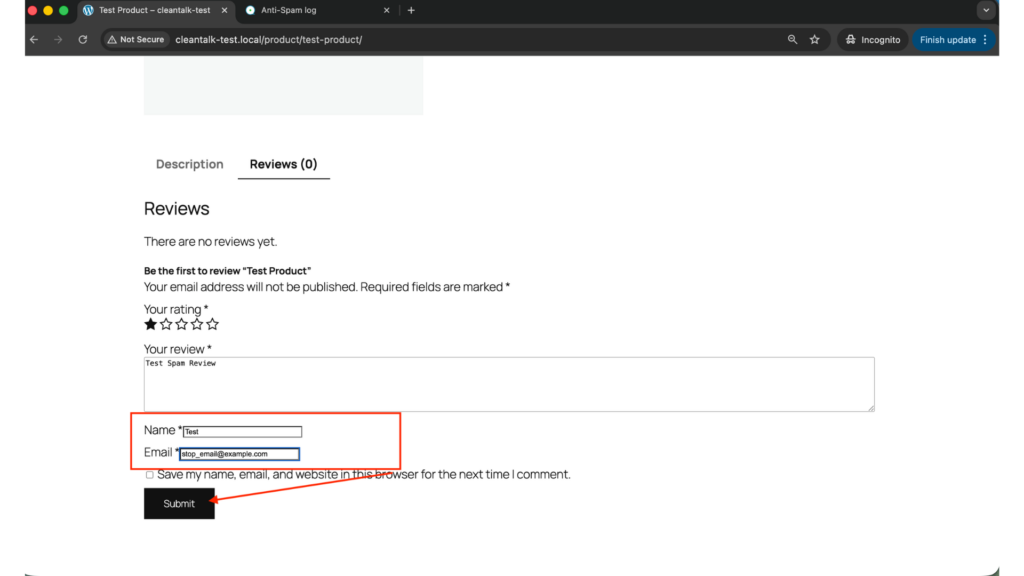
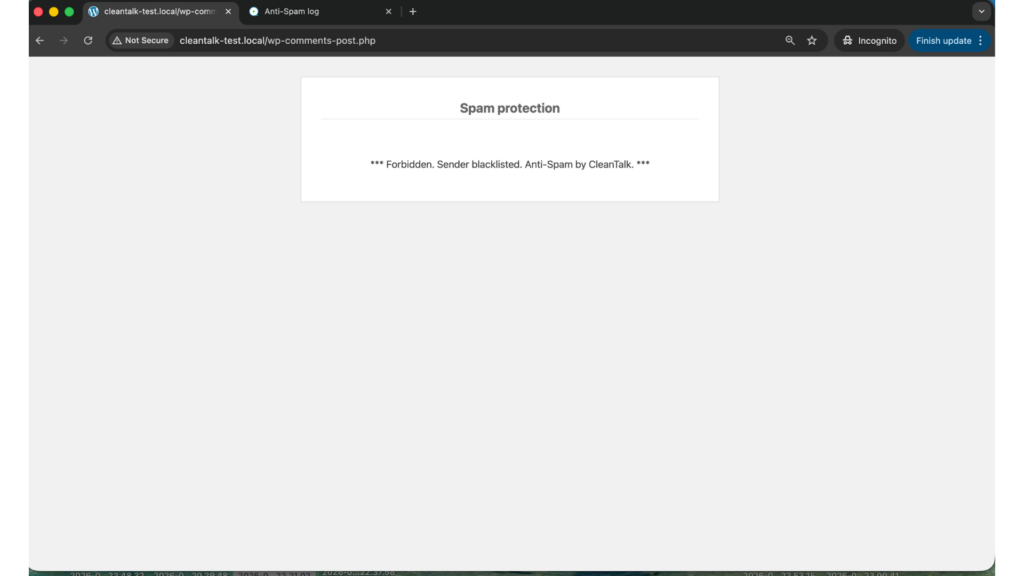
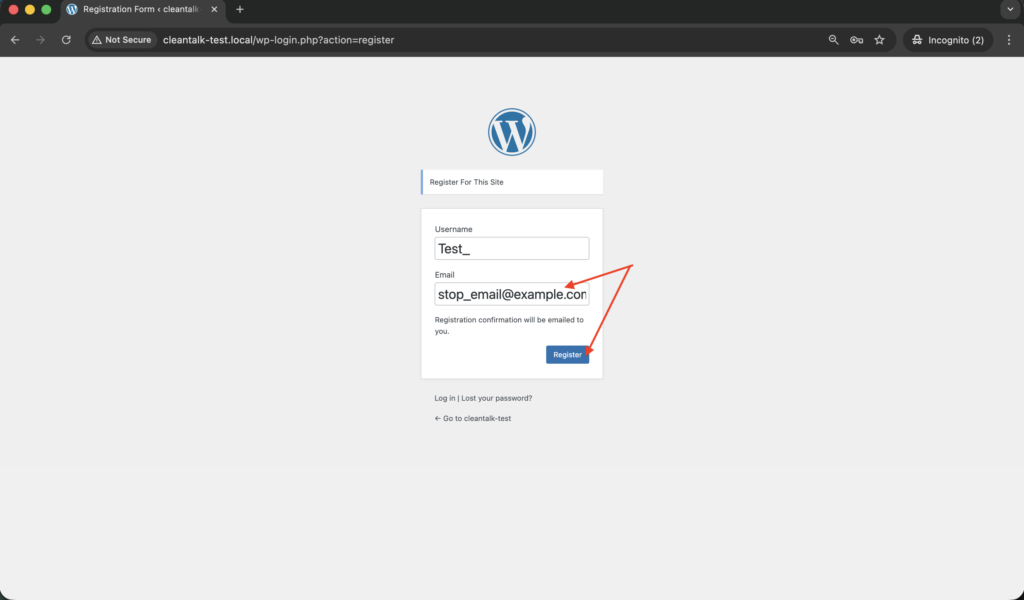
A simple way to test the setup is to use the following test address:
stop_email@example.com
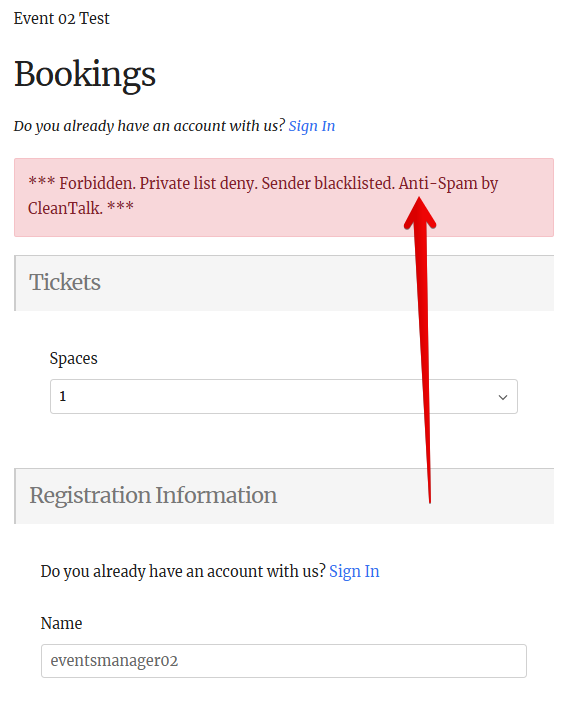
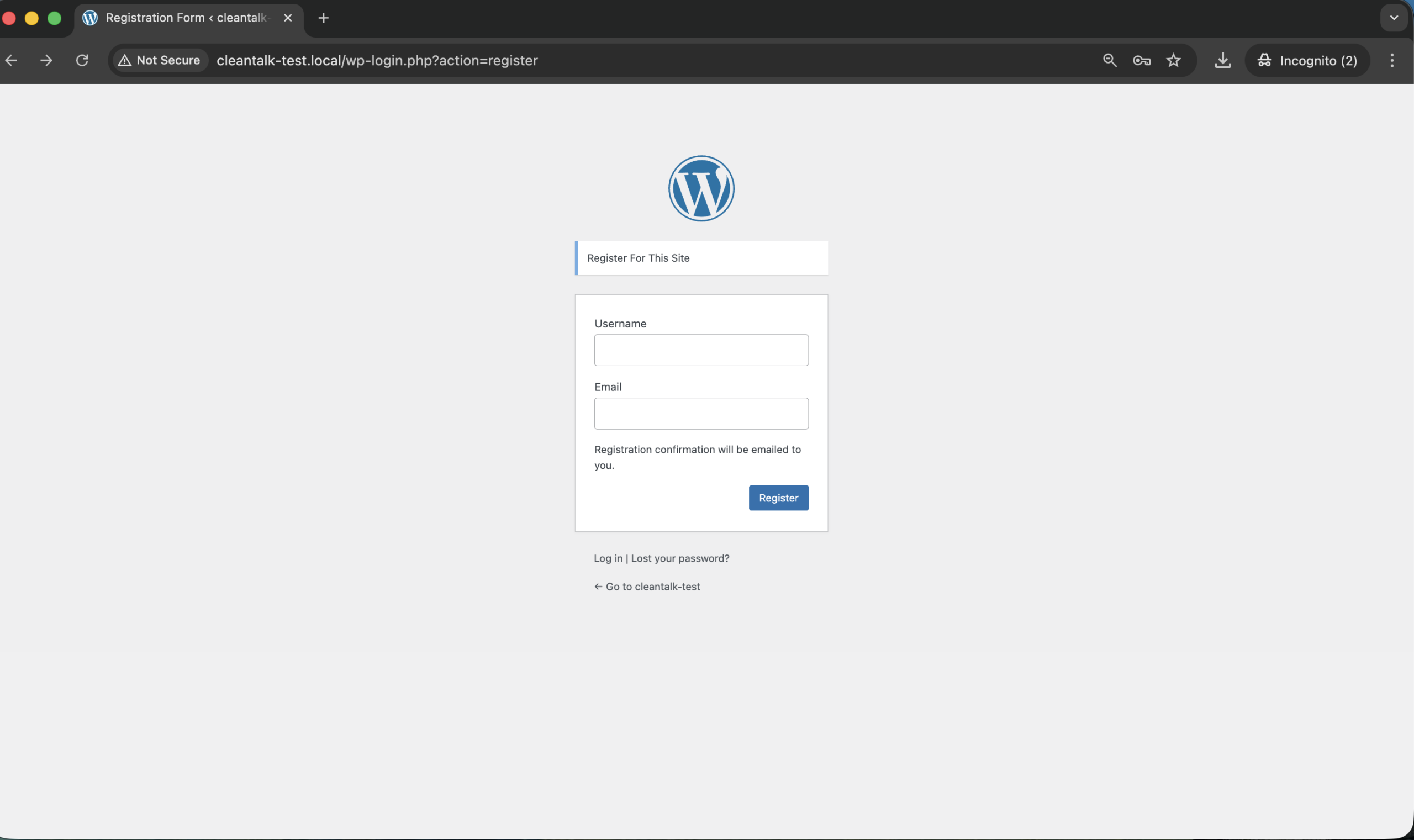
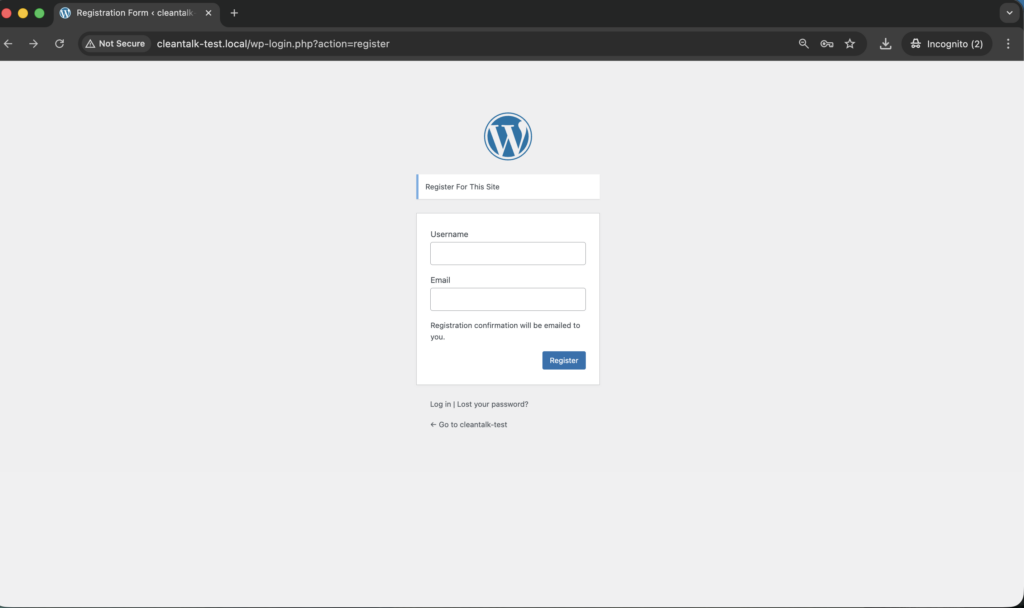
Open a forum page that allows registration or posting in an Incognito or private browser window.
Try to register or submit content using that email address.
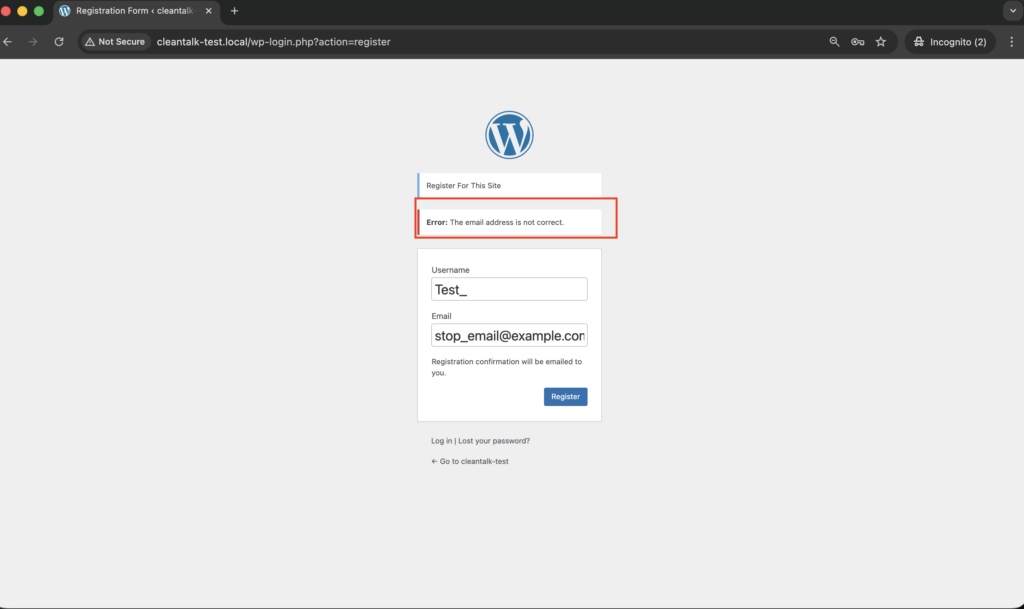
*** Forbidden. Sender blacklisted. Anti-Spam by CleanTalk. ***
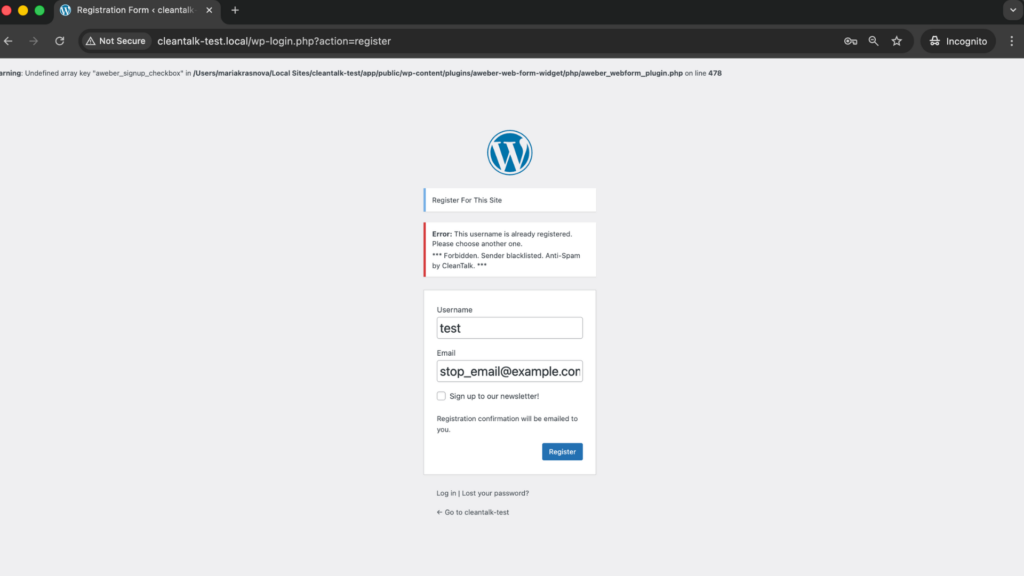
If everything is configured properly, the registration or submission should be blocked or should not appear as normal forum activity.
When testing, check both sides of the process:
- the frontend, to see whether the action is accepted
- the forum itself or user list, to verify that the spam action did not become a normal account, topic, or reply
This matters because a request can appear to go through on the surface while the real question is whether it was actually accepted into the community workflow.
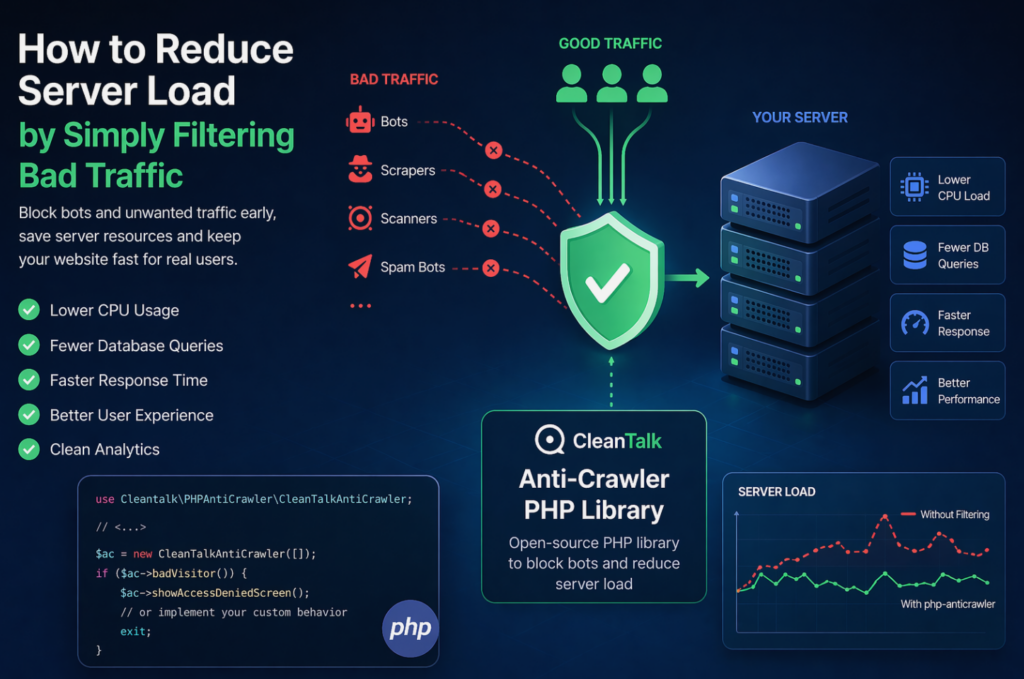
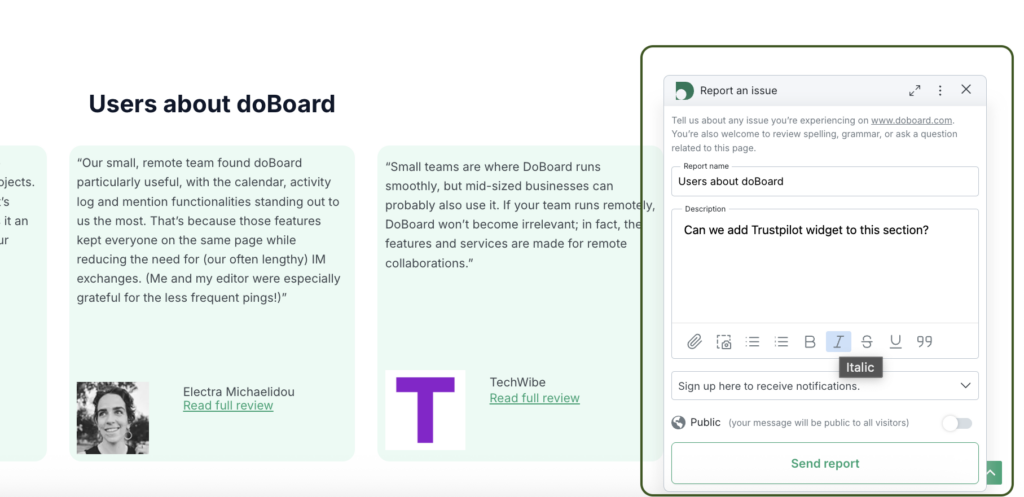
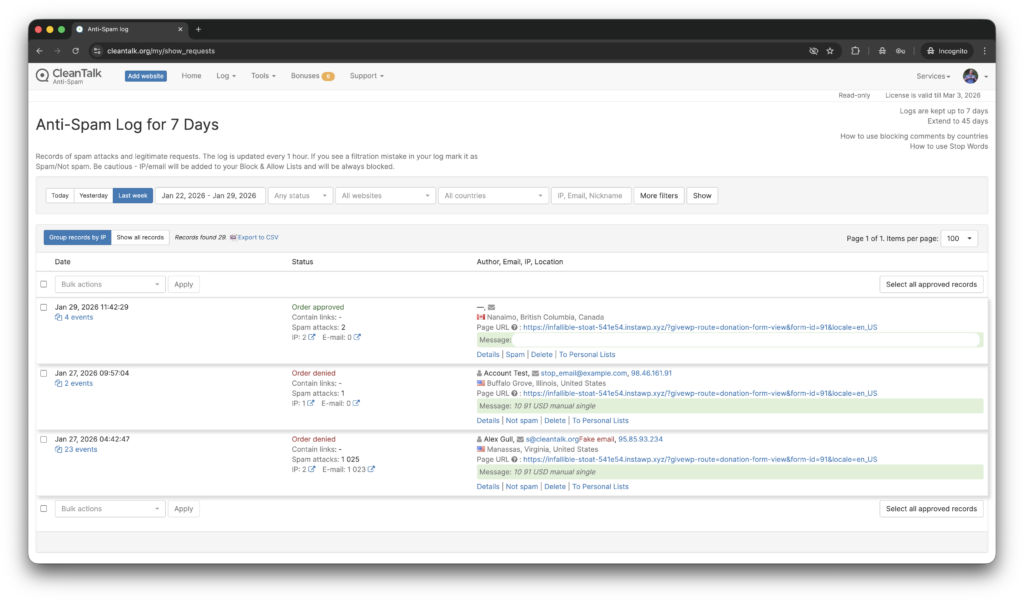
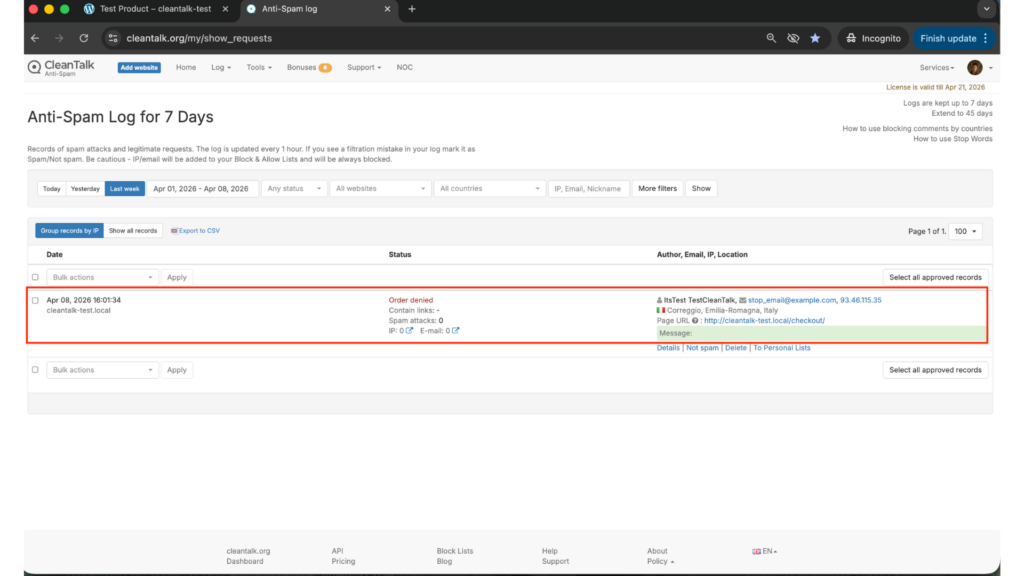
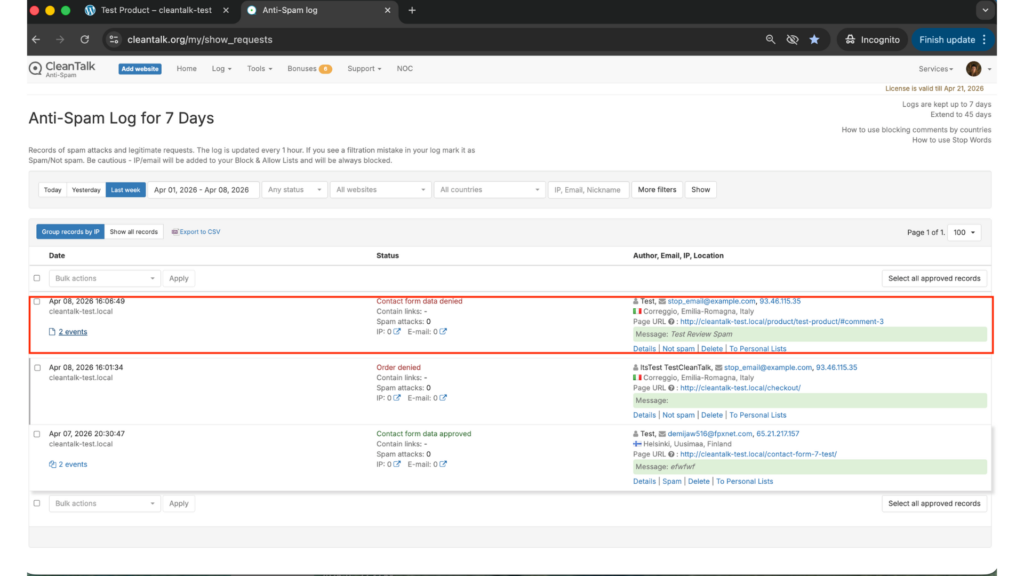
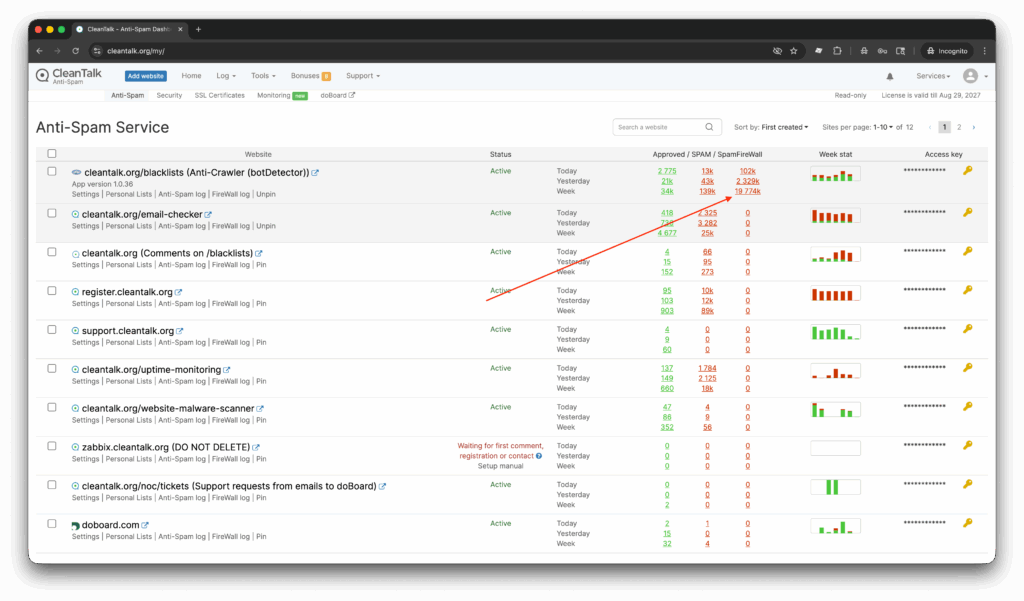
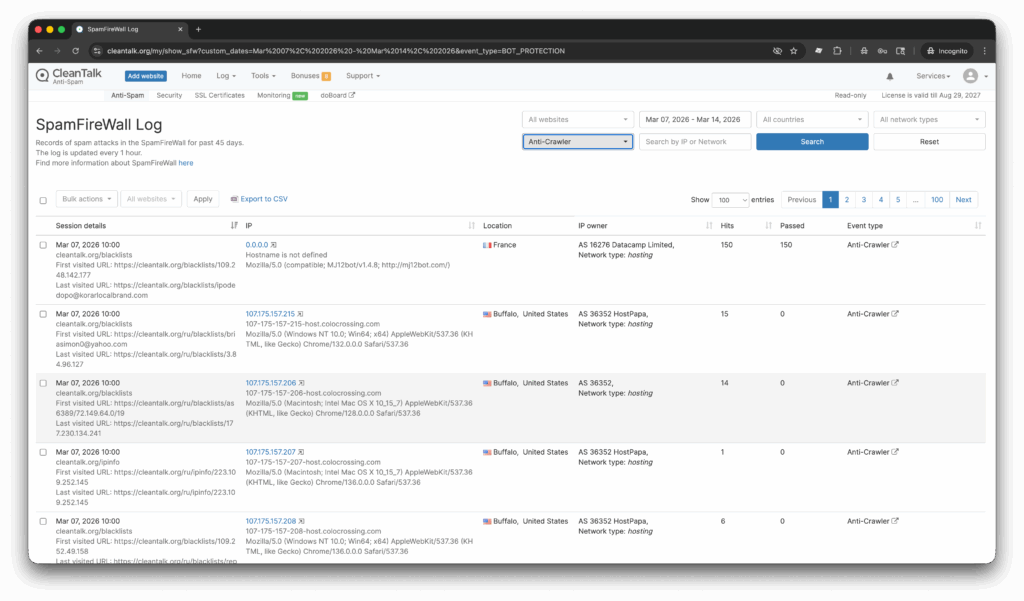
Cloud Dashboard and Monitoring
Blocking spam is only one part of the job. Good protection also gives you visibility into what is happening.
In the anti-spam dashboard, it is useful to review:
- sender IP and email
- submission time
- source page
- approval or denial status
- the likely reason a request was flagged
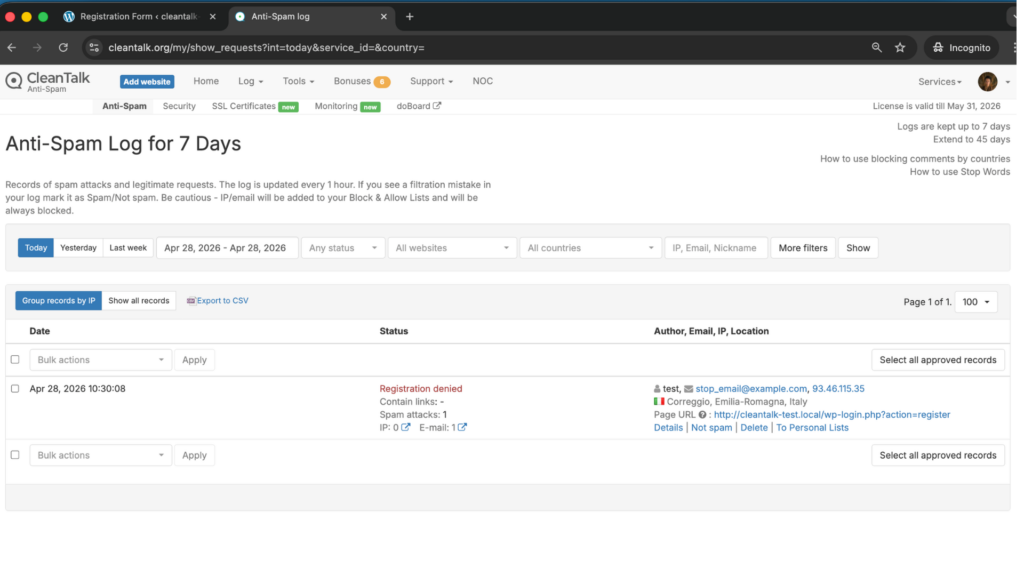
This makes it easier to spot recurring spam waves, identify weak areas of the site, and understand whether the biggest problem is registrations, topics, or replies.
That visibility helps you adjust the setup over time instead of guessing.
CAPTCHA, Forum Permissions, and Additional Anti-Spam Options
Besides CleanTalk, Asgaros Forum also supports or works with several additional anti-spam measures.
Guest Posting and Permissions
Asgaros Forum includes guest postings, moderators, permissions, usergroups, approval, banning, and reporting among its documented features. That means one of the simplest ways to reduce spam is to tighten who can post, who can create topics, and whether new users or guests should have the same permissions as trusted members.
This is especially useful when:
- you want to reduce anonymous spam
- you want to restrict topic creation to registered users
- you want more control over what new accounts can do
CAPTCHA for Guests
Asgaros Forum does not offer a simple built-in CAPTCHA switch for guest posting. According to the plugin FAQ, adding CAPTCHA to the guest editor requires a separate WordPress CAPTCHA plugin and custom hook-based logic in functions.php.
That makes CAPTCHA possible, but not a simple built-in checkbox setting.
Approval, Banning, and Reporting
Asgaros Forum also includes approval, banning, and reporting features in its documented feature set. These are useful as moderation and cleanup layers when the goal is not just to block spam automatically, but also to keep the forum manageable after suspicious activity happens.
Why Asgaros Forum Spam Becomes a Bigger Problem Over Time
Forum spam is not just a temporary nuisance. It tends to become a community and moderation problem.
Once junk registrations and low-quality posts start slipping through, they can:
- clutter forum sections
- push real discussions down
- reduce trust in the community
- increase manual moderation work
This is especially important on forums, where the visible quality of the discussion space affects whether real users want to participate.
Comparison of Anti-Spam Approaches for Asgaros Forum
| Solution | Main role | Strengths | Limitations | Best use case |
| CleanTalk | Core site-level anti-spam filtering | Filters suspicious registrations and submissions before they become normal forum activity, works without classic CAPTCHA friction | Usually strongest when combined with permissions or moderation rules | Sites that want the main anti-spam layer to protect forum quality |
| Guest posting and permissions | Built-in access control | Lets you reduce anonymous or low-trust posting, useful for restricting high-risk actions | Does not filter spam automatically by itself | Forums that want tighter control over who can post or create topics |
| Third-party CAPTCHA for guests | Extra anti-bot checkpoint | Can add an additional barrier against automated posting | Not a native one-click Asgaros setting and requires third-party plugin plus hook-based logic | Sites that specifically need a CAPTCHA layer for guest posting |
| Approval, banning, and reporting | Moderation and cleanup layer | Helps control abuse, remove bad actors, and review suspicious activity | Mostly reactive rather than preventive | Communities that need human moderation support |
In practice, the strongest starting point is to use one reliable primary anti-spam layer and then add tighter permissions or moderation controls only where they are truly needed.
Frequently Asked Questions
What is Asgaros Forum in WordPress?
Asgaros Forum is a WordPress plugin that adds a lightweight discussion board to a website. Its official WordPress.org page lists features such as profiles, notifications, uploads, polls, guest postings, approval, banning, reporting, moderators, permissions, and usergroups.
Why do Asgaros Forum sites get spam?
Because forums create several public entry points at once. Registrations, guest posts, new topics, and replies can all become targets for bots and manual spammers if they are not protected well.
Does Asgaros Forum have built-in CAPTCHA for guests?
Not as a simple native toggle. The official FAQ says that adding CAPTCHA to the guest editor requires a third-party WordPress CAPTCHA plugin and custom hook-based logic in functions.php.
Can CleanTalk protect Asgaros Forum without CAPTCHA?
Yes. CleanTalk can work as a site-level anti-spam layer for WordPress submissions and help reduce spam registrations and forum-related spam without forcing users through classic CAPTCHA challenges. CleanTalk’s plugin page describes it as CAPTCHA-free protection for forms, registrations, and broader submission types.
What is the best spam protection setup for Asgaros Forum in 2026?
For most websites, the best setup is to use CleanTalk as the main filtering layer, then tighten guest posting or forum permissions where needed, and use approval, banning, and reporting as moderation support. CAPTCHA can be added for guests, but it requires a separate plugin and custom integration.
Recommended Anti-Spam Stack for Asgaros Forum (2026)
| Use case | Recommended setup | Why it works |
| Standard community forum | CleanTalk as the main anti-spam filtering layer + tighter guest posting rules | Helps block obvious spam and reduce low-quality public activity |
| Member-focused forum | CleanTalk as the main anti-spam filtering layer + stricter permissions for new users | Reduces spam registrations and limits abuse from low-trust accounts |
| Guest-post-enabled forum | CleanTalk as the main anti-spam filtering layer + optional third-party CAPTCHA for guests + moderation rules | Balances stronger protection with support for anonymous participation |
| High-traffic public forum | CleanTalk as the main anti-spam filtering layer + approval, banning, and reporting workflow | Helps keep visible discussions cleaner and makes abuse easier to manage |
| Forums with recurring abuse patterns | CleanTalk as the main anti-spam filtering layer + usergroup and permission restrictions | Adds stronger control where spam follows repeatable behavior |
Final Thoughts
No single anti-spam tool can stop every kind of unwanted activity in Asgaros Forum.
Some controls are better at restricting who can post. Others are better at reviewing abuse after it happens. The most reliable approach is to combine one strong primary anti-spam layer with the forum’s own permission and moderation features.
For most WordPress websites using Asgaros Forum, the strongest setup is to use CleanTalk as the main site-level anti-spam layer, then tighten guest posting and permissions where necessary, and use approval, banning, and reporting tools to support moderation. Asgaros Forum itself documents those community-control features, while its FAQ makes clear that CAPTCHA for guests requires third-party integration rather than a built-in one-click setting.
This combination helps reduce spam registrations, protect discussions, and keep the forum more useful for real members.