-
How to Reduce Server Load by Simply Filtering Bad Traffic
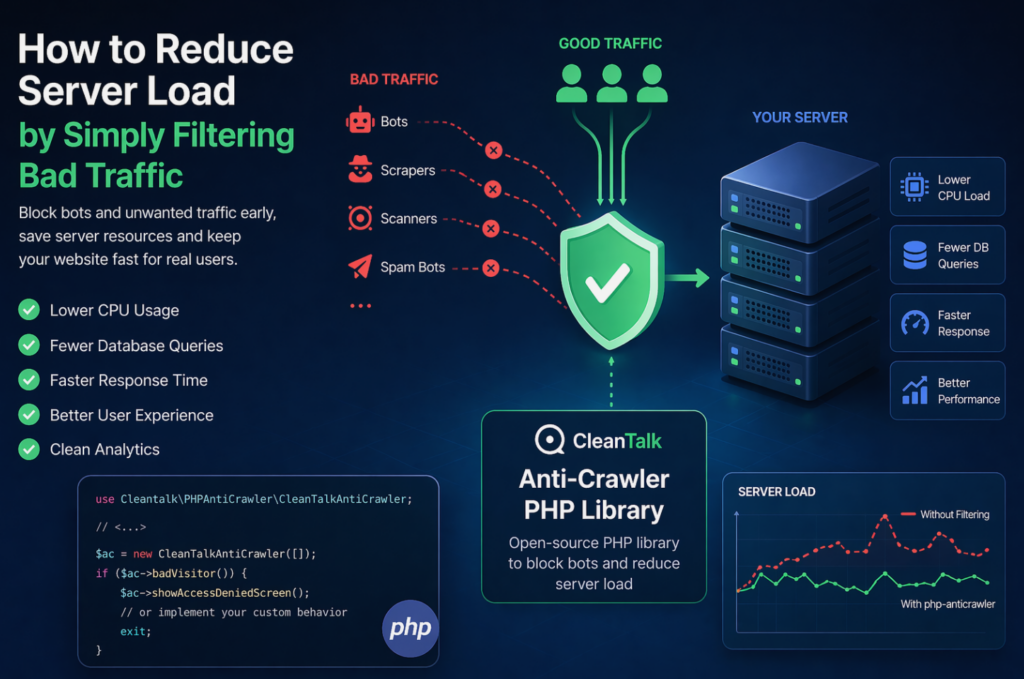
When a website starts slowing down, many teams immediately think about scaling infrastructure: adding CPU, RAM, more servers, or optimizing the database. In reality, a significant part of server load is often caused not by real users, but by automated traffic — bots, scrapers, vulnerability scanners, spam robots, and aggressive crawlers. These requests may continuously
FEEDBACK LOG
The Latest
-
otujoye@mailcorplrtgood.com — Detection and Blocking
What Is This Bot? The email address belongs to a set of randomized domains generated for automated use. As a result, it does not correspond to a legitimate mailbox and is therefore used for automated form submissions. In practice, log data shows repeated, high-frequency submission attempts, which are typically associated with domains lacking valid MX…
-
Spam Bot dinanikolskaya99@gmail.com — How to Block It and Stop Website Attacks
The email address dinanikolskaya99@gmail.com has been reported for sending spam and launching automated malicious requests on thousands of websites. According to CleanTalk BlackLists, this address has: The bot is currently blacklisted in CleanTalk Anti-Spam databases. What Does This Spam Bot Do? This spam bot employs a multilingual approach, sending seemingly innocent pricing inquiry messages in various languages…
-
Critical Vulnerability in WP Reset – Plaintext License Key Exposure via Public Log File (CVE-2025-10645)
CleanTalk Research Team has identified a severe information disclosure vulnerability in the popular WordPress plugin WP Reset (400,000+ active installations). The issue allows unauthenticated attackers to obtain license keys and sensitive site metadata directly from a publicly accessible log file created by the plugin. This vulnerability has been assigned CVE-2025-10645 and independently confirmed by Wordfence.…
-
Critical Vulnerability CVE-2025-11705: Arbitrary File Reading in Anti-Malware Security and Brute-Force Firewall
The CleanTalk research team discovered a critical vulnerability in the popular WordPress plugin “Anti-Malware Security and Brute-Force Firewall” (GOTMLS), installed on over 100,000 websites. CVE-2025-11705 allows attackers with minimal privileges (Subscriber level) to read arbitrary files on the server, including the critical wp-config.php file, which contains database credentials and secret keys. This issue was independently…

